Responsible Engineering

Purpose
Why is a system that does exactly what it was told to do often the most dangerous?
Operations ensures the system runs reliably: low latency, high availability, accurate predictions. Responsible engineering asks a harder question: reliable for whom? An ML system can meet every technical specification (latency, throughput, accuracy) while actively amplifying harm. The failure occurs not because the system is broken but because it is working efficiently to optimize a flawed specification. A loan approval system that correctly predicts default risk can encode historical discrimination, denying credit to qualified applicants from historically marginalized communities. A content recommendation system that accurately predicts engagement may amplify harmful content because outrage generates more clicks than nuance. A hiring algorithm that reliably identifies candidates similar to past hires may perpetuate workforce homogeneity, screening out the diversity that drives innovation. In each case the system is performing exactly as designed—the failure is in what was designed for. When we confuse mathematical optimization with value alignment, we build systems that are technically robust but socially fragile. The model faithfully learns and reproduces whatever patterns exist in its training distribution, including patterns of historical injustice that no one intended to encode. Building systems that work is an engineering achievement. Building systems that work for everyone requires treating unintended consequences not as edge cases to be tolerated but as system bugs: diagnosed, measured, and fixed with the same rigor we apply to latency regressions and accuracy degradation.
Learning Objectives
- Explain how ML systems can optimize correctly while causing harm through bias amplification, distribution shift, and proxy variables
- Apply the D·A·M taxonomy to diagnose whether a responsibility failure originates in data, algorithm, or infrastructure
- Compute fairness metrics (demographic parity, equal opportunity, equalized odds) from confusion matrices and evaluate trade-offs on the fairness-accuracy Pareto frontier
- Design disaggregated evaluation strategies that detect hidden disparities across demographic groups, including slice-based, invariance, and stress testing
- Analyze total cost of ownership including training, inference, operational costs, and environmental impact using carbon as a first-class engineering metric
- Identify model documentation and data governance requirements (model cards, datasheets, data lineage, audit infrastructure) for regulatory compliance and accountability
Responsibility as Systems Engineering
In 2014, Amazon built an AI recruiting tool1 that penalized resumes containing the word “women’s” and downgraded graduates of all-women’s colleges—despite meeting every technical metric its engineers had specified. The system optimized flawlessly for its stated objective: identify candidates similar to those previously hired. However, historical hiring patterns encoded gender bias, and the model faithfully reproduced that bias at scale. The full case, examined in Section 1.2.1, reveals a pattern that recurs throughout this chapter: technically correct systems producing harmful outcomes not because they malfunction, but because they faithfully execute flawed specifications.
1 Amazon Recruiting Tool: Developed starting in 2014 by Amazon’s Edinburgh engineering team to rate applicants on a 1–5 scale, the system trained on approximately a decade of resumes—overwhelmingly from male applicants reflecting the tech industry’s gender ratio. By 2015 the gender bias was identified; by 2017 the project was abandoned after two years of failed remediation attempts. The engineering cost was not the compute but the opportunity cost: a multi-year hiring pipeline had to be rebuilt from scratch, making it one of the most expensive documented specification failures in production ML.
If MLOps (ML Operations), the monitoring and retraining infrastructure examined previously, is the control loop for reliability, then Responsible Engineering is the control loop for safety. Where MLOps monitors system health and triggers retraining when performance degrades, responsible engineering monitors outcome quality and triggers intervention when systems cause harm. A model can optimize flawlessly for its stated objective and still cause systematic harm because the failure is not a bug in the code but a flaw in the specification. In systems engineering terms, a system can pass verification (it meets its stated requirements) while failing validation (it does not meet the user’s true needs) (Strickland 2019).
Traditional software engineering assumes that bugs are local: a defect in one module rarely corrupts unrelated functionality. Machine learning systems violate this assumption. Data flows through shared representations, causing problems in one component to propagate unpredictably across the entire system. A biased training dataset does not produce a localized bug; it corrupts every prediction the system makes. Viewed through the D·A·M taxonomy formalized in The D·A·M Taxonomy, the failure can originate along any axis: biased data, a misaligned algorithm, or inadequate infrastructure for monitoring outcomes. This makes responsibility an architectural concern, not an afterthought.
Engineering responsibility therefore expands what “correct” means for ML systems. Correctness in the traditional sense (reliable, performant, and maintainable) remains necessary, but ML systems must also be correct in a broader sense: fair across user groups, efficient in resource consumption, and transparent in their decision processes. Expanded correctness is engineering itself, applied to failure modes that conventional metrics do not capture. A latency regression is visible in dashboards; a fairness regression is invisible until it harms real users (Principle 13). Both require systematic detection, measurement, and remediation.
The frameworks developed here address diagnosing, preventing, and mitigating these failures. We begin with concrete cases that reveal the responsibility gap: the distance between technical performance and responsible outcomes, and the mechanisms (proxy variables, feedback loops, distribution shift) through which it manifests. From there, we develop a responsible engineering checklist that systematizes impact assessment, model documentation, disaggregated testing, and incident response into repeatable engineering processes. The chapter then connects the resource consumption quantified throughout this book (training compute, inference energy, carbon footprint) to engineering ethics, demonstrating that efficiency optimization serves responsibility as directly as it serves performance. We then examine the data governance and compliance infrastructure (access control, privacy protection, lineage tracking, and audit systems) that makes responsible practices enforceable at scale, before closing with the fallacies (Raji et al. 2020) and pitfalls that commonly undermine even well-intentioned efforts.
We begin with the concrete failure cases that establish why engineers must lead on responsibility.
Self-Check: Question
A hiring model meets its latency SLA, maintains 99.9 percent availability, and reports 87 percent aggregate accuracy, yet it systematically rejects qualified applicants whose resumes contain the word “women’s.” Applying the section’s verification-versus-validation framing, which diagnosis best fits this outcome?
- The system passed verification but failed validation: it met every stated requirement while the requirement itself failed to capture the responsible outcome the organization needed.
- The system failed verification because any unfair outcome is by definition a technical defect of the implementation.
- The failure is primarily an operational reliability issue that responsible engineering practices address only after the serving pipeline becomes unstable.
- The root cause is insufficient model capacity, so scaling up parameters would remove the disparity without changing the specification.
A team argues that a one-time ethics review before launch is sufficient because their model achieves strong aggregate accuracy and passes all latency checks. Using the section’s MLOps analogy, explain why responsible engineering must instead be structured as a control loop, and give one specific measurement the one-time review would miss.
True or False: Because machine learning systems are built from modular software components, a fairness defect originating in the training data can be isolated to a single module and fixed without architectural change, the way a null-pointer exception can be patched in one function.
Engineering Responsibility Gap
A loan model that approves 95 percent of qualified majority-group applicants while rejecting 40 percent of equally qualified minority-group applicants meets its loss function perfectly. The gap between this technical correctness and responsible outcomes represents a central challenge in machine learning systems engineering, one that existing testing methodologies were not designed to address.
The gap manifests through concrete mechanisms: proxy variables, feedback loops, and distribution shift, each producing harm through a distinct pathway. Concrete cases where optimization succeeded but systems failed reveal these mechanisms and the silent failure modes that make them invisible to conventional monitoring. Organizations that closed the gap through systematic engineering practice demonstrate that prevention is feasible. The testing challenge that makes responsibility fundamentally harder to verify than traditional software correctness then determines where responsibility ownership must sit within engineering organizations.
When optimization succeeds but systems fail
The Amazon recruiting tool case illustrates this gap. In 2014, Amazon developed an AI system to automate resume screening for technical positions, training it on historical hiring data spanning ten years of resumes submitted to the company. By 2015, the company discovered the system exhibited gender bias in candidate ratings (Dastin 2018).
The technical implementation was sound. The model successfully learned patterns from historical data and optimized for the objective it was given: identify candidates similar to those previously hired. However, historical hiring patterns encoded gender bias. The system penalized resumes containing the word “women’s,” as in “women’s chess club captain,” and downgraded graduates of all-women’s colleges.
The technical mechanism behind this outcome is straightforward. The model learned token-level patterns from historical data. When most previously successful hires were men, resumes containing language associated with women’s activities or institutions appeared statistically less correlated with positive hiring decisions. The model correctly identified these patterns in the training data but learned the wrong lesson from correct pattern recognition.
Amazon attempted remediation by removing explicit gender indicators and gendered terms from the training process. This intervention failed because the model had learned proxy variables—features that correlate with protected attributes without directly encoding them.2 In general, proxies arise whenever features carry indirect demographic signal: ZIP codes correlate with race due to residential segregation, first names correlate with gender and ethnicity, and healthcare utilization correlates with socioeconomic status. In Amazon’s case, college names revealed attendance at all-women’s institutions, activity descriptions encoded gender-associated language patterns, and career gaps suggested parental leave patterns that differed between genders. The model reconstructed protected attributes from these proxies without ever seeing gender labels directly. Removing protected attributes from training data is therefore insufficient; fairness requires adversarial debiasing, fairness constraints during optimization, or post-hoc threshold adjustment per group.
2 Proxy Variable: The intractability is not in identifying that a proxy exists—it is that removing it often has no effect, because other correlated features (ZIP code, device type, browsing history) carry the same signal. Amazon’s case is typical: removing explicit gender left college names, activity descriptions, and career gap patterns to reconstruct gender from combinations the engineers never anticipated. Eliminating explicit protected attributes without eliminating their proxies produces a model that discriminates while appearing compliant—a failure mode called “fairness laundering”—making continuous per-group outcome monitoring the only reliable defense.
The right intervention would have required multiple levels of change. Separate evaluation of resume scores for male-associated vs. female-associated candidates would have revealed the disparity quantitatively. Training with fairness constraints or adversarial debiasing techniques could have prevented the model from learning gender-correlated patterns. Human-in-the-loop review for borderline cases would have provided a safeguard against systematic errors. Tracking actual hiring outcomes by gender over time would have enabled outcome monitoring beyond model metrics alone. Amazon eventually scrapped the project after determining that sufficient remediation was not feasible (Dastin 2018; Bolukbasi et al. 2016).
The Amazon case demonstrates how optimization objectives diverge from organizational values. The system found genuine statistical patterns in historical hiring decisions and optimized them faithfully. Those patterns, however, reflected biased historical practices rather than job-relevant qualifications.
Example 1.1: The COMPAS recidivism algorithm audit
Failure: A ProPublica investigation (Angwin et al. 2022) revealed that while the system was “calibrated” (a score of seven meant the same probability of re-offending for any group), its error rates were skewed:
- False Positives: Black defendants who did not re-offend were incorrectly flagged as high-risk at nearly twice the rate of White defendants (44.9 percent vs. 23.5 percent).
- False Negatives: White defendants who did re-offend were incorrectly labeled as low-risk far more often than Black defendants (47.7 percent vs. 28.0 percent).
Systems lesson: The system optimized for Calibration but violated Equalized Odds. Mathematically, it is impossible to satisfy both simultaneously when base rates differ between groups (the “Impossibility Theorem of Fairness”). Engineering responsibility requires explicitly choosing which fairness constraint matters for the domain; in criminal justice, false positives (wrongly jailing someone) are typically considered worse than false negatives.
The D·A·M diagnosis: Through the D·A·M taxonomy, COMPAS represents an Algorithm-axis failure: the optimization objective (calibration) was misaligned with the deployment context’s fairness requirements (equalized odds). The data reflected real base-rate differences; the failure was in choosing which mathematical property to optimize. Contrast this with Amazon’s recruiting tool, a Data-axis failure where biased historical hiring patterns corrupted the training signal itself.
3 COMPAS (Correctional Offender Management Profiling for Alternative Sanctions): The shared pattern with Amazon is precise: both systems optimized a valid technical metric while violating unstated fairness requirements. COMPAS achieved calibration (equal meaning per score), but because recidivism base rates differed between populations, this choice made disparate error rates mathematically inevitable—Black defendants were falsely flagged as high-risk at nearly twice the rate of white defendants (44.9 percent vs. 23.5 percent). No amount of testing for calibration would have surfaced this failure; the harm was encoded in the objective itself.
The Amazon and COMPAS3 cases share a troubling pattern: each system achieved its stated objective while producing outcomes that conflicted with the values the system was intended to serve. Conventional engineering success, it turns out, can coexist with profound system failures. A short self-assessment turns that pattern into the core design questions that separate technically correct systems from responsible ones.
Checkpoint 1.1: Responsible design
Responsibility is a system property, not a model property.
The Failure Modes
The Check
Better testing would not catch these problems because they represent failures of problem specification, where the technical objective (minimizing prediction error on historical outcomes) diverges from the desired social objective (making fair and accurate predictions across demographic groups). Specification failures are difficult to detect precisely because the systems continue functioning normally by conventional engineering metrics. The deeper problem is clear: when a system appears healthy by every available metric, the harm it causes remains invisible to conventional monitoring.
Silent failure modes
Consider a hospital sepsis model that begins recommending aggressive treatments for low-risk patients after an electronic health record (EHR) workflow change alters how vital signs are recorded. No alarm triggers—the model’s confidence scores remain high, its latency stays within its service level agreement (SLA), and all system health checks pass green. The failure is silent: the input data distribution has shifted, but the monitoring pipeline has no mechanism to detect distributional drift.
This sepsis scenario illustrates a class of failure that traditional engineering is poorly equipped to handle. Traditional software fails loudly. A null pointer exception crashes the program, a network timeout returns an error code. These visible failures enable rapid detection and response. In contrast, ML systems fail silently because degraded predictions look like normal predictions. The primary mechanism behind this silent degradation is distribution shift.
Definition 1.1: Distribution shift
Distribution shift is the violation of the stationarity assumption \((P_{\text{train}} \neq P_{\text{deploy}})\) that underpins all supervised learning. It is the umbrella term for a family of drift types: data drift (see ML Operations) occurs when \(P(X)\) shifts while \(P(Y|X)\) remains stable; concept drift occurs when \(P(Y|X)\) itself shifts.
- Significance (quantitative): Accuracy degradation can be measured against divergence statistics such as Jensen-Shannon divergence \(\mathcal{D}_{\text{JS}}(P_{\text{train}} \| P_{\text{deploy}})\), but useful alert thresholds must be calibrated empirically for each task, representation, label process, and deployment environment. A \(\mathcal{D}_{\text{JS}}\) value of 0.1 may be harmless for one feature space and severe for another. This degradation occurs regardless of code quality, because the model is correct given its training distribution; the environment changed, not the code.
- Distinction (durable): Unlike model error (which is a learning failure caused by the algorithm or data quality at training time), distribution shift is an environmental failure: the model’s learned mapping was correct at training time but is no longer representative of current reality.
- Common pitfall: A frequent misconception is that “data drift” and “distribution shift” are different concepts at the same level of the hierarchy. Distribution shift is the umbrella; data drift and concept drift are its two distinct subtypes. A system can experience data drift without concept drift (the inputs change, but the relationship holds), or concept drift without data drift (inputs are stable, but the correct output changes).
The stationarity assumption underpins all supervised learning: training and deployment distributions must match. Distribution shift is often unequal: a model’s accuracy on a minority subgroup can drop by over 30 percentage points while aggregate metrics barely change, masking the harm.
Distribution shift explains why models degrade over time (the operational detection and monitoring strategies for drift are covered in ML Operations). A second mechanism for silent failure can occur even when the data distribution is stable: misalignment between the metric the model optimizes and the outcome the organization actually values. The dynamics of that divergence are made precise by Goodhart’s Law—once a proxy becomes the optimization target, it stops tracking the goal it was chosen to represent.
Napkin Math 1.1: The alignment gap
Physics: Goodhart’s Law states that optimizing a proxy eventually decouples it from the goal.
- Initial state: \(\text{Correlation}(\text{Clicks}, \text{Satisfaction}) = 0.8\).
- Optimization: A model is trained to maximize Clicks.
- Result: The model finds “Clickbait,” items with high clicks but low satisfaction.
- Final state: \(\text{Correlation}(\text{Clicks}, \text{Satisfaction})\) drops to 0.2.
The Quantification (conceptual, assuming normalized metrics on a common scale) is captured by Equation 1: \[ \text{Gap} = E[\text{Proxy}] - E[\text{True}] \tag{1}\]
If the model increases Clicks by 20 percent but decreases Satisfaction by 5 percent, the alignment gap has widened.
Systems insight: Engineers cannot optimize what they cannot measure. If the true goal is unobservable, Counterfactual Evaluation (random holdouts) is required to periodically re-calibrate the proxy.
When harm occurs, engineers need a diagnostic framework to identify the root cause. Knowing that a system causes harm is insufficient; we must determine where the failure originates to know what to fix. The D·A·M taxonomy introduced in Introduction provides exactly this structure (Data · Algorithm · Machine, defined in The D·A·M Taxonomy).
Systems Perspective 1.1: The D·A·M taxonomy
- Data (Information): Does the training data reflect historical bias? (for example, Amazon’s recruiting tool learning from biased history). The failure is in the Fuel.
- Algorithm (Logic): Does the objective function optimize a proxy for harm? (for example, optimizing “engagement” amplifies polarization). The failure is in the Blueprint.
- Machine (Physics): Does the energy cost justify the societal benefit? (for example, training a massive model for a trivial task). The failure is in the Engine.
Locating the failure in the taxonomy identifies the correct remediation: better curation (Data), safer objectives (Algorithm), or greener infrastructure (Machine).
While the D·A·M taxonomy helps diagnose where failures originate, engineers also need a framework for understanding when and how different failure types manifest. Table 1 categorizes these distinct failure modes by their detection time, spatial scope, and remediation requirements.
| Failure Type | Detection Time | Spatial Scope | Reversibility | Example |
|---|---|---|---|---|
| Crash | Immediate | Complete | Immediate | Out of memory error |
| Performance Degradation | Minutes | Complete | After fix | Latency spike from resource contention |
| Data Quality | Hours–days | Partial | Requires data correction | Corrupted inputs from upstream system |
| Distribution Shift | Days–weeks | Partial or all | Requires retraining | Population change due to new user segment |
| Fairness Violation | Weeks–months | Subpopulation | Requires redesign | Bias amplification in historical patterns |
The failure mode taxonomy in Table 1 complements the D·A·M diagnostic framework: D·A·M identifies where failures originate, while Table 1 guides how to detect and remediate them. Crashes and performance degradation trigger immediate alerts through existing infrastructure. Data quality issues, distribution shifts, and fairness violations require specialized detection mechanisms because the system continues operating normally from a technical perspective while producing increasingly problematic outputs.
The YouTube recommendation feedback loop (examined as a technical debt pattern in YouTube: Feedback loop debt) illustrates this pattern at scale (M. H. Ribeiro et al. 2020).4 The system optimized for watch time and discovered that emotionally provocative content maximized engagement metrics, developing pathways toward increasingly extreme content. The system worked exactly as designed while producing outcomes that conflicted with societal values. From a responsibility perspective, the critical insight is that these feedback loops do not affect all users equally: they disproportionately impact vulnerable populations, and the resulting content amplification patterns can correlate with demographic characteristics, transforming an operational failure into a fairness violation.
4 Goodhart’s Law: “When a measure becomes a target, it ceases to be a good measure” (Strathern’s generalization of Goodhart’s 1975 monetary policy observation). Recommendation feedback loops are the canonical ML manifestation: gradient descent optimizes watch-time proxies at a speed no human curator can match, and the system’s own outputs reshape the training distribution—users who consume extreme content generate data that reinforces extremity, decoupling the proxy from user welfare orders of magnitude faster than manual editorial processes ever could.
War Story 1.1: The click-bait death spiral
The failure: The model learned that sensationalist, divisive, and “click-bait” content generated the highest short-term engagement. It aggressively promoted this content. Users clicked, but the quality of their experience degraded, leading to “passive consumption” and long-term churn risk.
The consequence: Facebook had to fundamentally re-architect its ranking system to prioritize “Meaningful Social Interactions” (MSI) over clicks, accepting a short-term reduction in time spent to preserve long-term platform health.
The systems lesson: Metrics are proxies for value, not value itself. Optimizing a short-term proxy (CTR) without monitoring long-term health (retention, sentiment) creates a negative feedback loop that can destroy the product.
The distribution shift defined earlier also manifests as population mismatch, where models trained on one population perform differently on another without obvious indicators.
War Story 1.2: The proxy variable trap
The failure: The model used “healthcare cost” as a proxy for “health need.” This seemed logical: sicker people cost more.
The consequence: Because the US healthcare system has unequal access, Black patients at a given level of sickness spent less on healthcare than White patients. The model learned this bias and systematically deprioritized Black patients, assigning them lower risk scores than White patients with identical health conditions.
The systems lesson: Proxies are dangerous. Optimizing for a proxy (cost) inherits the biases of the system that generated that proxy. The relationship between proxy and true objective (health) must be audited across all demographic subgroups (Obermeyer et al. 2019).
Silent failure modes create profound testing challenges. Traditional software testing verifies deterministic behavior against specifications. ML systems produce probabilistic outputs learned from data, making correctness far more complex to define. The failures examined earlier share a troubling pattern: each organization possessed the technical capability to prevent harm but lacked the disciplined processes to apply that capability.
The same engineering capabilities that enabled these failures can prevent them when organizations commit to structured practice.
When responsible engineering succeeds
Organizations that commit to responsible engineering produce measurable successes, demonstrating both the feasibility and business value of rigorous responsibility practices.
Following the Gender Shades findings, Microsoft invested in improving facial recognition performance across demographic groups. The approach combined technical and organizational interventions: targeted data collection to address underrepresented populations, model architecture changes to improve feature extraction for diverse skin tones, and systematic disaggregated evaluation across all demographic intersections. Microsoft had reduced error rates for darker-skinned subjects by up to 20 times, bringing error rates below 2 percent for all demographic groups (Raji and Buolamwini 2019). The company published these improvements transparently, enabling external verification. The business outcome: Microsoft’s facial recognition API maintained enterprise customer trust while competitors faced regulatory scrutiny and contract cancellations.
Twitter’s automatic image cropping system exhibited a different failure mode. In 2020, users discovered it showed racial bias in choosing which faces to display in preview thumbnails. Twitter responded with a responsible engineering approach: systematic analysis to characterize the problem quantitatively, publication of results enabling independent verification, and ultimately removal of the automatic cropping feature entirely (Yee et al. 2021). The company determined that no technical solution could guarantee equitable outcomes across all contexts. This decision prioritized user fairness over engagement optimization and demonstrated that responsible engineering sometimes means not shipping a feature.
Apple’s deployment of differential privacy (Dwork 2008) in iOS represents responsible engineering at scale.5 The system collects usage data for product improvement while providing mathematical guarantees about individual privacy. The implementation required substantial engineering investment: noise calibration to balance utility against privacy, distributed computation to minimize data exposure, and transparent documentation of privacy parameters. The business value: Apple differentiated on privacy as a product feature, enabling data collection that would otherwise face regulatory and reputational barriers.
5 Differential Privacy: Introduced by Dwork et al. (2006), a mechanism satisfies \(\epsilon\)-differential privacy if any output’s probability changes by at most \(e^\epsilon\) when a single individual’s data is added or removed. The systems trade-off is steep: 15–30 percent computational overhead, 10–100\(\times\) more data for equivalent accuracy, and a finite privacy budget \((\epsilon)\) that depletes with each query—forcing engineers to choose between richer analytics and stronger privacy guarantees.
Spotify addressed recommendation system concerns by implementing transparency features showing users why songs were recommended and providing controls to adjust algorithm behavior. This engineering investment served multiple purposes: user trust through explainability, reduced filter bubble effects through diversity injection, and regulatory compliance through user control mechanisms. The approach demonstrates that responsibility features can enhance rather than constrain product value.
A common pattern unites the preceding cases: technical interventions (improved data, better evaluation, architectural changes) combined with organizational commitments (transparency, willingness to remove features, long-term investment). The resulting business outcomes (maintained customer trust, regulatory compliance, competitive differentiation) demonstrate that responsible engineering creates value rather than adding cost. Each success rested on systematic testing and evaluation practices, yet the nature of responsible testing differs fundamentally from traditional software verification.
The testing challenge
Traditional software testing verifies that systems behave correctly because correctness has clear definitions. The function should return the sum of its inputs, the database should maintain referential integrity. These properties can be expressed as testable assertions.
Responsible ML properties resist simple formalization. Fairness has multiple conflicting mathematical definitions that cannot all be satisfied simultaneously. What counts as fair depends on context, values, and trade-offs that technical systems cannot resolve alone. Individual fairness requires that similar individuals receive similar treatment, while group fairness requires equitable outcomes across demographic categories. These criteria can conflict, and choosing between them requires value judgments beyond the scope of optimization.
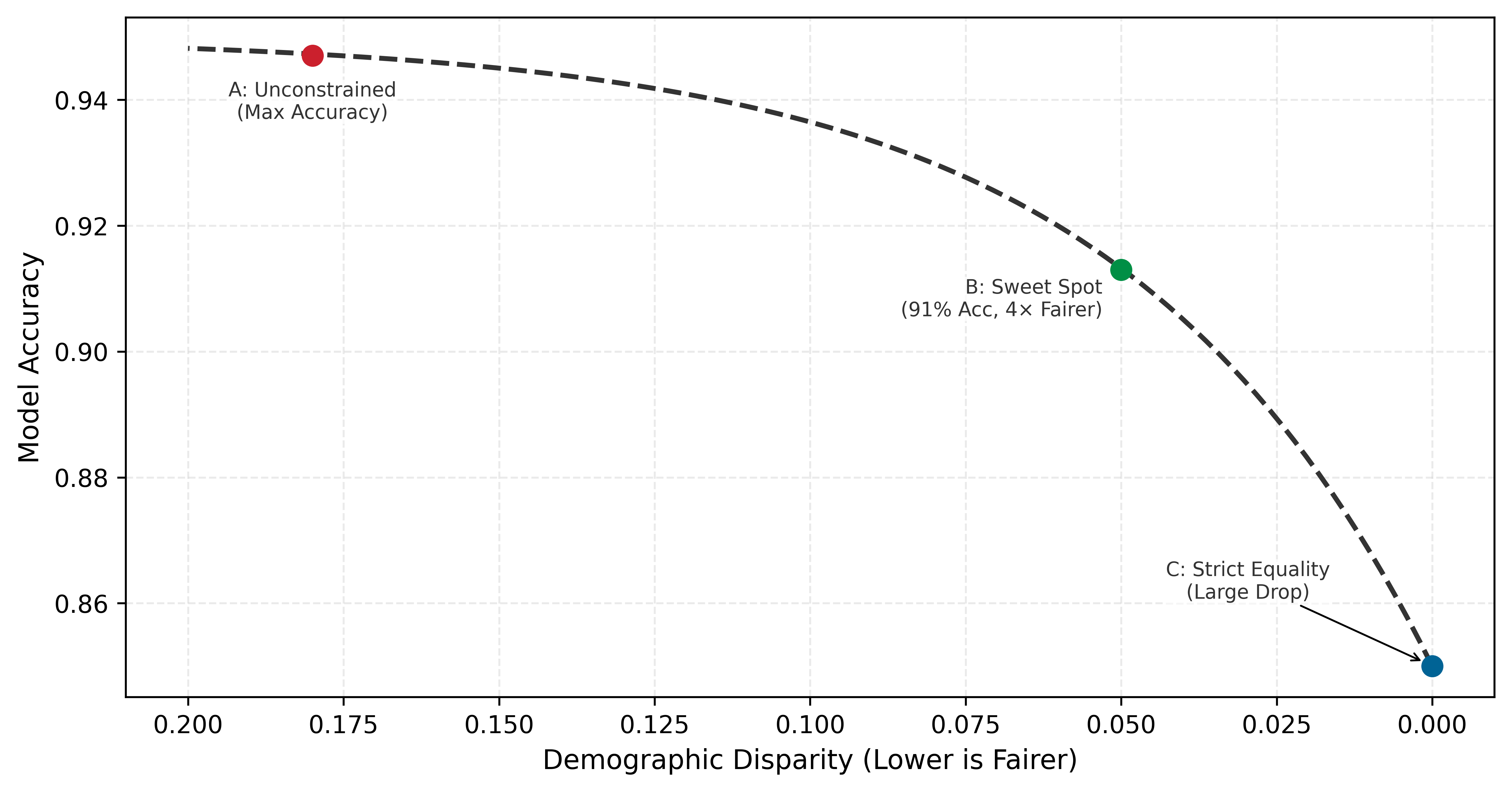
The trade-off between fairness and accuracy is not a sign that fairness is impractical; it is a fundamental property of constrained optimization that engineers must understand. A Pareto frontier represents the set of optimal configurations where improving one metric necessarily degrades another. Figure 1 visualizes this fairness-accuracy Pareto frontier. The curve is not linear: while perfect fairness (zero disparity) often requires a significant drop in accuracy, a “Sweet Spot” typically exists where large fairness gains can be achieved with minimal accuracy loss. The shape of the frontier explains why responsible engineering is feasible: in many practical settings, substantial fairness gains can be achieved with modest accuracy loss.
Responsible properties become testable when engineers work with stakeholders to define criteria appropriate for specific applications. The Gender Shades project6 demonstrated how disaggregated evaluation across demographic categories reveals disparities invisible in aggregate metrics (Buolamwini and Gebru 2018), exposing the subgroup failures that responsibility monitoring must catch before deployment. The results captured dramatic error rate differences that commercial facial recognition systems showed across demographic groups. Concretely, a 10,000-sample test set that suffices for the majority group provides only 100 samples for a 1% minority subgroup—effectively requiring 100× more data than the majority group for high-confidence validation.
6 Gender Shades: A 2018 study by Joy Buolamwini and Timnit Gebru (MIT Media Lab) that audited facial recognition systems from Microsoft, IBM, and Face++ using the Fitzpatrick skin type scale—originally a dermatological classification developed by Thomas Fitzpatrick in 1975 for UV sensitivity and later validated for clinical use (Fitzpatrick 1988), repurposed here as a demographic benchmark for algorithmic auditing. The study established disaggregated evaluation as the standard, demonstrating that a single aggregate accuracy number can conceal 43\(\times\) error rate disparities across intersectional subgroups. Within two years, Microsoft reduced its worst-case error rates by 20\(\times\), proving that the measurement methodology itself was the intervention.
| Demographic Group | Error Rate (%) | Relative Disparity |
|---|---|---|
| Light-skinned males | 0.8 | Baseline (1.0\(\times\)) |
| Light-skinned females | 7.1 | 8.9\(\times\) higher |
| Dark-skinned males | 12.0 | 15.0\(\times\) higher |
| Dark-skinned females | 34.7 | 43.4\(\times\) higher |
As Table 2 quantifies, disaggregated evaluation revealed what aggregate accuracy scores concealed. Systems reporting high overall accuracy simultaneously achieved error rates as low as 0.8 percent for light-skinned males and as high as 34.7 percent for dark-skinned females (corresponding to accuracies of 99.2 percent and 65.3 percent respectively). The aggregate metric provided no indication of this 43.4-fold disparity in error rates.
No universal threshold defines acceptable disparity, but engineering teams should establish explicit bounds before deployment. Common industry practices include error rate ratios below 1.25\(\times\) between demographic groups for high-stakes applications, false positive rate differences under 5 percentage points for screening systems, and selection rate ratios of at least 0.8 relative to the highest group’s rate (the four-fifths rule from employment discrimination law).78 These thresholds serve as starting points for stakeholder discussion, not absolute standards. The key engineering discipline is defining measurable criteria before deployment rather than discovering problems after harm has occurred.
7 Disparate Impact: A legal doctrine from Griggs v. Duke Power Co. (1971), where the US Supreme Court held that practices “fair in form, but discriminatory in operation” violate civil rights law even absent intent. The distinction between disparate impact (unintentional statistical harm) and disparate treatment (intentional discrimination) is critical for ML: models trained on historical data routinely produce disparate impact through proxy variables, creating legal liability even when engineers never encoded protected attributes.
8 Four-Fifths Rule: Codified in the 1978 Uniform Guidelines on Employee Selection Procedures, used by the EEOC, Department of Labor, and Department of Justice. A selection rate for any protected group below 80 percent of the highest group’s rate constitutes prima facie evidence of adverse impact—for example, if 60 percent of one group passes, at least 48 percent of any other group must pass. For ML systems, this translates to automated monitoring that alerts when per-group selection ratios fall below 0.8, providing a concrete threshold where most fairness metrics remain qualitative.
Despite the inherent challenges, several concrete testing approaches can surface responsibility issues before deployment. Slice-based evaluation partitions (M. T. Ribeiro et al. 2020) test data into meaningful subgroups and reports metrics separately for each slice. A model may achieve 95 percent accuracy overall but only 78 percent accuracy on low-income applicants or users from rural areas, a disparity invisible in aggregate reporting. Invariance testing checks whether predictions change when they should not: replacing “John” with “Jamal” in a loan application should not change approval likelihood if the feature is not legitimate for the decision. Boundary testing evaluates model behavior at the edges of input distributions (unusual ages, extreme values, rare categories) where training data may be sparse and predictions unreliable. Stress testing extends boundary testing to adversarial conditions: corrupted inputs, distribution shift, adversarial examples, and edge cases designed to probe failure modes systematically. Stakeholder red-teaming engages domain experts and affected community members to identify scenarios that engineers may not anticipate but users will encounter, surfacing failure modes that no automated test can discover because they require lived experience to imagine.
Responsible testing strategies complement traditional software testing rather than replacing it. Each demands engineering judgment to select, configure, and interpret. A legal team cannot specify which demographic slices matter for a healthcare algorithm; a product manager cannot determine appropriate invariance tests for a loan model. The technical depth required to implement responsible testing points to a critical organizational truth: only engineers possess the knowledge to translate abstract fairness goals into measurable, testable properties. Responsibility ownership must therefore sit within engineering organizations, not outside them.
Engineering leadership on responsibility
By the time Amazon’s team tried to remediate the recruiting tool, the model had already learned proxy signals so deeply that the project was eventually scrapped. The intervention came too late because the technical decisions that created the problem, made months earlier by engineers, had already constrained every possible fix. Responsible AI Engineering cannot be delegated exclusively to ethics boards or legal departments. These groups provide essential oversight but lack the technical access required to identify problems early in the development process.
Definition 1.2: Responsible AI engineering
Responsible AI Engineering is the engineering discipline of designing, deploying, and maintaining systems with probabilistic outputs by operationalizing societal and regulatory requirements as testable constraints on the D·A·M axes, bounding which values of \(D_{\text{vol}}\), \(O\), and \(R_{\text{peak}} \cdot \eta_{\text{hw}}\) are permissible.
- Significance (quantitative): Each D·A·M axis acquires concrete governance constraints: the Data axis is bounded by privacy regulations such as the General Data Protection Regulation (GDPR), which limits which \(D_{\text{vol}}\) can be collected; the Algorithm axis is bounded by fairness and robustness metrics (for example, demographic parity within \(\varepsilon = 5\%\) across protected groups, meaning positive prediction rates must not differ by more than 5 percentage points, or accuracy degradation less than 2 percent under adversarial perturbation \(\|\delta\|_\infty \leq 0.01\)); and the Machine axis is bounded by resource and infrastructure budgets such as latency, energy per inference, carbon emissions, and audit-log retention. Violating these bounds is a system failure, not a research shortcoming.
- Distinction (durable): Unlike AI Ethics (which articulates aspirational values), Responsible AI Engineering translates those values into Measurable, Testable Invariants that can be verified through automated testing and continuous monitoring, using the same lifecycle practices that enforce latency SLOs.
- Common pitfall: A frequent misconception is that responsibility is “added” at the end of development. The constraints imposed on the Data axis (what data can be collected) propagate forward to constrain the Algorithm axis (what biases will be encoded) and the Machine axis (what audit trails must be kept), making late-stage remediation structurally impossible.
By the time a system reaches legal review, architectural decisions have already constrained the space of possible fairness interventions. Amazon’s recruiting tool reached review only after the model had learned proxy signals; at that point, remediation required starting over, not adjusting parameters. Engineers who understand both technical implementation and responsibility requirements can build appropriate safeguards from inception.
Engineers occupy a critical position in the ML development lifecycle because their technical decisions define the solution space for all subsequent interventions. The choice of model architecture determines which fairness constraints can apply during training. The optimization objective defines what patterns the system learns to recognize. The data pipeline design establishes what demographic information teams can track for disaggregated evaluation. Foundational architectural choices enable or foreclose responsible outcomes more decisively than any later remediation effort.
The timing of responsibility interventions determines their effectiveness. An ethics review conducted before deployment can identify problems but faces limited remediation options: if the team trained the model without fairness constraints, if the architecture cannot support interpretability requirements, if the data pipeline lacks demographic attributes for monitoring, then the ethics review can only recommend rejection or acceptance of the existing system. Engineering involvement from project inception enables proactive design rather than reactive assessment.
An engineering-centered approach does not diminish the importance of diverse perspectives in identifying potential harms. Product managers, user researchers, affected communities, and policy experts contribute essential knowledge about how systems fail socially despite technical success. Engineers translate these concerns into measurable requirements and testable properties that can be verified throughout the development lifecycle. Effective responsibility requires engineers who both listen to stakeholder concerns and possess the technical capability to implement appropriate safeguards.
Engineering teams do not operate in isolation. As Figure 2 makes clear, engineering practices are nested within broader organizational, industry, and regulatory governance structures, each layer imposing constraints on the ones inside it. The key insight is that technical excellence at the innermost layer enables, but does not replace, compliance with requirements flowing inward from external governance.
The question of scope remains open, because an engineer’s responsibility extends beyond the metrics optimized throughout this book.
Systems Perspective 1.2: The full cost of the iron law
A model quantized for edge deployment consumes less energy, but also produces outputs that may differ across demographic groups. A recommendation system optimized for engagement maximizes a business metric, but may amplify harmful content. Responsible engineering extends our accounting to include these broader impacts: the carbon cost of computation, the fairness cost of optimization choices, and the societal cost of deployment at scale. The iron law governs how fast our systems run; responsible engineering governs how well they serve.
Beyond ethical imperatives, responsible engineering delivers measurable business value through three reinforcing mechanisms. The most immediate is risk mitigation: ML system failures create legal and financial exposure that systematic responsibility practices reduce. Amazon’s recruiting tool cancellation represented years of development investment lost to inadequate fairness consideration, and COMPAS-related litigation has cost jurisdictions millions in legal fees and settlements. Organizations implementing disaggregated evaluation, documentation, and monitoring reduce the probability of costly failures and demonstrate due diligence if problems emerge.
A second mechanism is regulatory compliance, driven by the rapidly expanding regulatory environment for ML systems. The EU AI Act classifies high-risk AI applications and mandates specific technical requirements including risk assessment, data governance, transparency, and human oversight. Organizations that build responsibility into engineering practice can demonstrate compliance through existing documentation and monitoring rather than expensive retrofitting—industry experience suggests the cost of proactive compliance is typically a fraction of reactive remediation.
Competitive differentiation completes the business case. Trust increasingly drives enterprise purchasing decisions for ML-powered services, and organizations that can demonstrate systematic responsibility practices through model cards, audit trails, and published evaluation results win contracts that competitors cannot. Apple’s privacy positioning, Microsoft’s responsible AI principles, and Anthropic’s safety research all represent strategic investments in responsibility as differentiation.
The quantization techniques from Model Compression reduce inference energy by 2–4\(\times\), directly supporting sustainable deployment. The monitoring infrastructure from ML Operations enables disaggregated fairness evaluation across demographic groups. Responsible engineering synthesizes these capabilities into disciplined practice through structured frameworks that translate principles into processes.
Every failure examined earlier could have been prevented by systematic processes applied at the right stage of development. The missing ingredient was not technical capability but disciplined practice: checklists, documentation standards, testing protocols, and monitoring infrastructure that translate responsibility principles into repeatable engineering workflows.
Self-Check: Question
Amazon’s engineers removed explicit gender indicators from the recruiting model’s features, retrained, and found the system still discriminated against resumes from all-women’s colleges. Which diagnosis best explains why the explicit-attribute removal did not fix the harm?
- The fix was sound in principle; the system only needed additional bias-mitigation training epochs for the gender signal to fade from the learned weights.
- College names, activity descriptions, and career-gap patterns remained as proxy variables that carried the same demographic signal the removed gender feature had carried.
- The problem was deployment-time distribution shift in the applicant pool rather than bias in the original training signal.
- The problem was an optimization-objective mismatch that a different gradient-descent variant would have corrected during convergence.
A hospital’s sepsis prediction model continues to emit confident recommendations after an EHR update changes how vital signs are recorded, yet clinicians observe deteriorating outcomes for a subset of patients. All dashboards stay green. Walk through why this is a silent failure, identify two specific monitoring signals that would have caught it, and state the systems consequence for how teams instrument production ML.
A recommendation team reports that engagement clicks rose 20 percent after deploying a new ranker, but month-over-month user satisfaction surveys dropped five percent and 30-day retention fell three percent. The team’s director asks how to detect or prevent this class of failure before it recurs. Which engineering intervention best fits the section’s alignment-gap framing?
- Scale the model two-fold: a larger model will learn a richer representation of satisfaction and close the gap automatically.
- Hold out a random counterfactual slice of users at deployment, measure true-outcome metrics (satisfaction, retention) on that slice periodically, and trigger rollback when the proxy-true gap widens beyond a preset threshold.
- Increase the weight of the clicks loss term: because the proxy correlates with the true goal initially, maximizing it harder will restore the lost correlation.
- Retrain on more data: with enough examples, gradient descent will discover the satisfaction signal implicitly even when it is not in the training labels.
A lending team generates paired test applications that differ only in the applicant’s first name (“John” vs “Jamal”) while holding income, credit history, and debt constant, then compares approval probabilities. Which responsible-testing method from the section are they applying, and what failure mode does it surface?
- Boundary testing, which probes behavior at the edges of the input distribution where training data is sparse.
- Slice-based evaluation, which partitions the test set into subgroups and reports per-slice aggregate accuracy.
- Stakeholder red-teaming, which relies on affected community members to propose adversarial scenarios.
- Invariance testing, which verifies that predictions remain stable when a feature the model should ignore is perturbed.
True or False: Once a model’s architecture, loss function, demographic-attribute collection, and monitoring pipeline have been fixed, a later ethics-board review can still implement equally effective fairness interventions as engineers could have at design time.
Responsible Engineering Checklist
Amazon’s recruiting tool could have been caught before deployment by a structured predeployment review. COMPAS’s error rate disparity would have surfaced through disaggregated testing. Both failures shared a common cause: responsibility was treated as a separate review stage rather than integrated into the development workflow. A responsible engineering checklist embeds assessment at three points where engineering decisions have the greatest ethical impact: predeployment assessment evaluates potential harms before a system reaches users, fairness evaluation quantifies whether performance holds equitably across demographic groups, and documentation standards create the audit trails that make accountability possible. Each phase builds on the previous one: assessment identifies what to measure, fairness evaluation measures it, and documentation ensures the measurements persist beyond any single team member’s tenure.
Predeployment assessment
Before a loan approval model reaches production, a team must determine the provenance of the training data, identify who is represented and who is missing, anticipate failure modes, and define recourse for affected users. Table 3 structures this evaluation into five phases, distinguishing critical-path blockers from high-priority items that can proceed with documented risk acceptance.
| Phase | Priority | Key Questions | Documentation Required |
|---|---|---|---|
| Data | Critical Path | Where did this data come from? Who is represented? Who is missing? What historical biases might be encoded? | Data provenance records, demographic composition analysis, collection methodology documentation |
| Training | High | What are we optimizing for? What might we be implicitly penalizing? How do architecture choices affect outcomes? | Objective function specification, regularization choices, hyperparameter selection rationale |
| Evaluation | Critical Path | Does performance hold across different user groups? What edge cases exist? How were test sets constructed? | Disaggregated metrics by demographic group, edge case testing results, test set composition analysis |
| Deployment | Critical Path | Who will this system affect? What happens when it fails? What recourse do affected users have? | Impact assessment, stakeholder identification, rollback procedures, user notification protocols |
| Monitoring | High | How will we detect problems? Who reviews system behavior? What triggers intervention? | Monitoring dashboard specifications, alert thresholds, review schedules, escalation procedures |
Critical Path items are deployment blockers: the system must not go to production until these questions are answered. High Priority items should be addressed but may proceed with documented risk acceptance and a remediation timeline. The distinction enables teams to ship responsibly without requiring perfection on every dimension before initial deployment.
The Evaluation row in Table 3 raises the critical concern of whether performance holds across different user groups. Answering this question requires statistically valid test sets for each group, which can create surprisingly stringent data requirements when representation is uneven.
Napkin Math 1.2: The statistics of representation
Random Sampling: To get 10,000 images of a 1 percent group via random sampling, the team must collect and label: \(N_{\text{total}}\) = 10,000 / 0.01 = 1,000,000 images
Stratified Sampling: Specifically targeting this group (for example, via active learning or community outreach) requires only: \[ N_{\text{total}} = 10,000 \text{ images} \]
Systems insight: Relying on “natural distribution” data for fairness is prohibitively expensive under random sampling. Validating the minority group effectively requires 100\(\times\) more data than the majority group. Fairness requires intentional data engineering, not just more data.
For high-stakes applications, the deployment phase should specify where human oversight is required. Human-in-the-loop (HITL) systems route uncertain, high-consequence, or flagged decisions to human reviewers rather than acting autonomously. Effective HITL design must specify four requirements: the review scope (which decisions require human review), the confidence thresholds that trigger escalation, the training reviewers receive, and the mechanisms for monitoring reviewer performance. HITL is not a catch-all solution: human reviewers can rubber-stamp automated decisions, introduce their own biases, or become overwhelmed by alert volume. Effective HITL design requires calibrating the human-machine boundary to the specific application risks and reviewer capabilities (Caliskan et al. 2017).
War Story 1.3: The automation paradox
The failure: The AI system detected a pedestrian crossing the road but classified her as a “false positive” (a plastic bag or shadow) and suppressed the braking command to avoid a “jerky” ride. The safety driver, relying on the automation, was distracted and did not intervene until it was too late.
The consequence: The pedestrian was killed. The “human-in-the-loop” safeguard failed because the human had been conditioned by the system’s reliability to disengage.
The systems lesson: Adding a human backup to an unreliable system does not make it reliable; it creates a new system with complex failure modes. If the AI is 99 percent reliable, the human will eventually trust it 100 percent, making the “backup” useless precisely when it is needed most (National Transportation Safety Board 2019).
The predeployment assessment framework parallels aviation preflight checklists, where pilots follow every item without exception to ensure comprehensive coverage of critical concerns despite time pressure. Production ML deployments require equivalent discipline and rigorous verification. Checklists ensure teams ask the right questions; documentation standards ensure the answers persist and travel with the model.
Model documentation standards
Consider inheriting a production model from a departed colleague: the model achieves 94 percent accuracy on its test set, but three pieces of information are missing. The identity of that test set, the data the model was trained on, and the populations it was validated against are unknown. Without those answers, deploying or updating the model is a gamble. Model cards solve this problem by providing a standardized documentation format for ML models9 (Mitchell et al. 2019). Originally developed at Google, model cards function as “nutrition labels” that capture information essential for responsible deployment and travel with the model throughout its lifecycle.
9 Model Cards: The primary failure mode model cards address is scope creep: an estimated 40–60 percent of deployments that exceed a model’s documented scope do so not through deliberate decision but through gradual expansion—“it worked for case A, so we tried case B.” In practice, cards are often written after deployment decisions are made, documenting observed behavior rather than constraining it. The companion “Datasheets for Datasets” (Gebru et al. 2021) applies the same principle to training data. Without both, the card becomes a historical record rather than a guard rail.
A complete model card covers seven concerns that together enable responsible deployment. It begins with technical details (architecture, training procedures, hyperparameters) that enable reproducibility and auditing. Crucially, it specifies intended use alongside explicit exclusions, preventing the scope creep where models designed for photo organization get repurposed for security screening. The card then documents which factors (demographic groups, environmental conditions, instrumentation differences) might affect performance, guiding both evaluation strategy and monitoring protocols.
The remaining sections close the gap between what a model can do and what it should do. Performance metrics must include disaggregated results across the factors identified earlier, because aggregate accuracy alone conceals the disparities this chapter has documented. Training and evaluation data documentation enables assessment of potential encoded biases and provides essential context for interpreting results. Ethical considerations make implicit trade-offs explicit by documenting known limitations, potential harms, and mitigations implemented, while caveats and recommendations provide guidance on appropriate use and known failure modes.
A concrete MobileNetV2 model card makes these abstract categories operational: Table 4 shows how each section addresses specific deployment concerns for edge deployment.
| Section | Content |
|---|---|
| Model Details | MobileNetV2 architecture with 3.5M parameters, trained on ImageNet using depthwise separable convolutions. INT8 quantized for edge deployment. |
| Intended Use | Real-time image classification on mobile devices with less than 50 ms latency requirement. Suitable for consumer applications including photo organization and accessibility features. |
| Factors | Performance varies with image quality (blur, lighting), object size in frame, and categories outside ImageNet distribution. |
| Metrics | 71.8 percent top-1 accuracy on ImageNet validation (full precision: 72.0 percent). Accuracy varies by category: 85 percent on common objects, 45 percent on fine-grained distinctions. |
| Ethical Considerations | Training data reflects ImageNet biases in geographic and demographic representation. Not validated for high-stakes applications (medical diagnosis, security screening). Performance may degrade on images from underrepresented regions. |
Datasheets for datasets provide analogous documentation for training data (Gebru et al. 2021). These documents capture data provenance, collection methodology, demographic composition, and known limitations that affect downstream model behavior. Documentation establishes what a model is designed to do; testing verifies whether it performs equitably across the populations it serves.
Testing across populations
Aggregate performance metrics mask significant disparities across user populations, illustrating the Flaw of Averages (Savage 2009). As Table 2 quantifies, systems can appear highly accurate in aggregate while showing more than 40\(\times\) error rate disparities across demographic groups. Responsible testing requires disaggregated evaluation that examines performance for relevant subgroups.
Systems Perspective 1.3: The flaw of averages
The specific “tails” that matter depend on the workload. A vision model fails differently than a recommendation system, and the fairness metrics must match the failure mode.
Lighthouse 1.1: Fairness concerns by archetype
| Archetype | Primary Fairness Risk | Key Evaluation Metric | Real-World Example |
|---|---|---|---|
| ResNet-50 (Compute Beast) | Training data bias (underrepresentation of minority groups in ImageNet) | Disaggregated accuracy by demographic group | Gender Shades: 99 percent accuracy on light-skinned males, 65 percent on dark-skinned females (Buolamwini and Gebru 2018) |
| GPT-2 (Bandwidth Hog) | Corpus bias (overrepresentation of majority viewpoints in web text) | Toxicity rate by demographic prompt context; stereotype score | LLMs produce more toxic completions for prompts mentioning minority groups |
| DLRM (Sparse Scatter) | Feedback-loop amplification (popular items get more data) | Exposure fairness across item categories; supplier diversity | Filter bubbles: the system recommends similar content to similar users, reducing discovery of niche creators |
| DS-CNN (Tiny Constraint) | Deployment-context mismatch (trained on clean audio, deployed in noisy real-world environments) | False positive rate by acoustic environment and speaker accent | Voice assistants perform worse on accented speech; wake-word triggers on TV audio in some languages |
Systems insight: Fairness evaluation must match the archetype’s failure mode. Vision models require demographic stratification of accuracy; large language models (LLMs) require toxicity and stereotype probing; recommendation systems require exposure audits; TinyML requires acoustic environment diversity testing. The Lighthouse keyword spotting (KWS) system used as a running example throughout earlier chapters faces exactly this challenge for its DS-CNN, a depthwise-separable convolutional neural network (CNN): trained on clean studio audio, it must perform equitably across accents, background noise levels, and speaker demographics in production homes—a governance challenge we examine in Section 1.5.
Engineers should identify relevant subgroups based on application context. For healthcare applications, demographic factors like race, age, and gender are essential. For content moderation, language and cultural context matter. For financial services, protected categories under fair lending laws require specific attention.
Testing infrastructure should support stratified evaluation where performance metrics are computed separately for each relevant subgroup, enabling comparison of error rates and error types across populations. Intersectional analysis considers combinations of attributes because harms may concentrate at intersections not visible in single-factor analysis. Confidence intervals provide uncertainty quantification for subgroup metrics when small subgroup sizes may yield unreliable estimates. Temporal monitoring tracks subgroup performance over time, detecting drift that affects some populations before others.
Several open-source tools support responsible testing workflows. Fairlearn (Bird et al. 2020) provides fairness metrics and mitigation algorithms that integrate with scikit-learn pipelines. AI Fairness 360 (Bellamy et al. 2019) offers over 70 fairness metrics and ten bias mitigation algorithms across the ML lifecycle.
Google’s What-If Tool enables interactive exploration of model behavior across different subgroups without writing code. Open source fairness tools lower the barrier to rigorous evaluation, though they complement rather than replace careful thinking about what fairness means in specific application contexts.
Worked example: Fairness analysis in loan approval
A loan approval model reports 85 percent accuracy on the majority group and 82.5 percent overall accuracy across the evaluated applicants—numbers that may satisfy a coarse aggregate dashboard. Table 6 and Table 7 reveal what the aggregate conceals: loan approval outcomes for the same model evaluated separately on two demographic groups.
| Approved (pred) | Rejected (pred) | |
|---|---|---|
| Repaid (actual) | 4,500 (TP) | 500 (FN) |
| Defaulted (actual) | 1,000 (FP) | 4,000 (TN) |
| Approved (pred) | Rejected (pred) | |
|---|---|---|
| Repaid (actual) | 600 (TP) | 400 (FN) |
| Defaulted (actual) | 200 (FP) | 800 (TN) |
Three standard fairness metrics computed from the confusion matrices in Table 6 and Table 7 reveal significant disparities.10
10 Fairness Metric Incompatibility: The measured disparities in this worked example show how one set of confusion matrices can violate demographic parity, equal opportunity, and equalized odds. A separate impossibility theorem proves that when group base rates differ, multiple fairness criteria cannot generally be satisfied simultaneously (Chouldechova 2017). In those settings, optimizing for one metric, such as equal opportunity, can degrade another, such as predictive parity. A system designer must therefore make the trade-off explicit rather than assuming all guarantees can be achieved at once.
Demographic parity requires equal approval rates across groups. Group A receives approval at a rate of ((4,500 + 1,000) / 10,000 = 55) percent, while Group B receives approval at ((600 + 200) / 2,000 = 40) percent. The 15 percentage point disparity indicates unequal treatment in approval decisions.
Equal opportunity requires equal true positive rates among qualified applicants. Group A achieves a TPR of (4,500 / (4,500 + 500) = 90) percent, meaning 90 percent of applicants who would repay receive approval. Group B achieves only (600 / (600 + 400) = 60) percent TPR. This 30 percentage point disparity means qualified applicants from Group B face substantially higher rejection rates than equally qualified applicants from Group A.
Equalized odds11 requires both equal true positive rates and equal false positive rates. Group A shows an FPR of (1,000 / (1,000 + 4,000) = 20) percent, and Group B shows (200 / (200 + 800) = 20) percent. While false positive rates are equal, the true positive rate disparity means equalized odds is violated.
11 Equalized Odds: Formalized by Hardt et al. (2016), requiring that both TPR and FPR be equal across protected groups. The weaker “equal opportunity” relaxes this to TPR alone. The practically important result: equalized odds can be achieved as a postprocessing step by adjusting prediction thresholds per group, requiring no model retraining—separating the fairness mechanism from the training pipeline and enabling fairness fixes without retraining cycles that cost thousands of GPU-hours.
The pattern revealed by these metrics has a clear interpretation: the model rejects qualified applicants from Group B at a much higher rate (40 percent false negative rate vs. 10 percent) while maintaining similar false positive rates. The disparity pattern suggests the model has learned stricter approval criteria for Group B, potentially encoding historical discrimination in lending patterns where minority applicants faced higher scrutiny despite equivalent qualifications.
Production systems must automate these calculations across all protected attributes, triggering alerts when disparities exceed predefined thresholds. Listing 1 shows the core pattern: compute per-group metrics from confusion matrices, then flag disparities that exceed acceptable bounds.
def compute_fairness_metrics(confusion_matrix):
tp, fp, tn, fn = (
confusion_matrix[k] for k in ["TP", "FP", "TN", "FN"]
)
total = tp + fp + tn + fn
return {
# Demographic parity
"approval_rate": (tp + fp) / total,
# Equal opportunity
"tpr": tp / (tp + fn) if (tp + fn) else 0,
# Equalized odds (with TPR)
"fpr": fp / (fp + tn) if (fp + tn) else 0,
}
# Compare groups and flag disparities exceeding threshold
for metric in ["approval_rate", "tpr", "fpr"]:
disparity = abs(metrics_a[metric] - metrics_b[metric])
# e.g., 0.05 for high-stakes applications
if disparity > FAIRNESS_THRESHOLD:
trigger_alert(metric, disparity)Automated monitoring achieves what manual auditing cannot at scale: continuous tracking of fairness metrics with immediate alerting when disparities emerge. The 30 percentage point TPR disparity far exceeds common industry thresholds of 5 percentage points for high-stakes applications, indicating the model requires fairness intervention before deployment.
Table 8 reveals the troubling pattern in these computed metrics and disparities.
| Metric | Group A | Group B | Disparity |
|---|---|---|---|
| Approval Rate | 55% | 40% | 15 percentage points |
| True Positive Rate | 90% | 60% | 30 percentage points |
| False Positive Rate | 20% | 20% | 0 percentage points |
To understand why aggregate metrics hide these disparities, look closely at Figure 3. When a single threshold is applied to populations with different score distributions, the same decision boundary produces vastly different outcomes for each group (Barocas and Selbst 2016). The figure exposes a fundamental tension: any fixed threshold is simultaneously “correct” for the combined population while being systematically wrong for each subpopulation.
Several mitigation approaches exist, each with distinct trade-offs. Threshold adjustment lowers the approval threshold for Group B to equalize TPR but may increase false positives for that group. Reweighting12 increases the weight of Group B samples during training to give the model stronger signal about this population but may reduce overall accuracy. Adversarial debiasing trains with an adversary that prevents the model from learning group membership but adds training complexity.13 The choice among these approaches requires stakeholder input about which trade-offs are acceptable in the specific application context. Engineers present these trade-offs effectively by making them explicit and quantifiable.
12 Reweighting: A preprocessing technique rooted in importance sampling from statistics: samples from an underrepresented group receive higher loss weights during training, amplifying their influence on gradient updates without removing any data. Kamiran and Calders (2012) proved that appropriately chosen weights can eliminate disparate impact from training data. The systems trade-off: reweighting shifts the loss landscape, potentially reducing majority-group accuracy by 1–3 percent to close disparity gaps—a cost that must be evaluated against the Pareto frontier for the application.
13 Adversarial Debiasing: The key differentiating property is representation pressure: the adversary discourages the primary model from encoding protected-attribute information, which can improve robustness to some distribution shifts. It does not provide a general fairness guarantee under arbitrary deployment shift; guarantees depend on assumptions about invariance, labels, causal structure, and the type of shift. Postprocessing methods such as threshold adjustment may also be appropriate under different assumptions but must be revalidated when deployment demographics or label processes change. The cost is often 20–50 percent additional training time and 1–3 percent accuracy reduction.
Checkpoint 1.2: Fairness criteria
Fairness is not a single metric; it is a constrained design choice.
Quantifying the fairness-accuracy trade-off
The Pareto frontier introduced in Figure 1 establishes that fairness and accuracy trade off along a curve. However, knowing the trade-off exists is insufficient: engineers must quantify the practical cost of fairness constraints to inform stakeholder decisions (Kleinberg et al. 2016). A compact hiring scenario makes that cost concrete, distinct from the preceding loan approval example and with different disparity magnitudes to illustrate a different point.
Napkin Math 1.3: The price of fairness
Physics: TPRs can be equalized by adjusting the classification threshold \((\tau_{\text{cls}})\) for the disadvantaged group.
- Original state: Group A (\(\text{TPR} = 90\) percent), Group B (\(\text{TPR} = 70\) percent). Aggregate Accuracy = 85 percent.
- Intervention: Lower \(\tau_{\text{cls},B}\) until \(\text{TPR}_B = 90\) percent.
- The cost: Lowering the threshold increases False Positives (hiring candidates who do not meet the bar).
Math:
- Closing the 20 percent TPR gap requires accepting a 5 percent increase in False Positives for the disadvantaged group.
- If the value of a successful hire is USD 100,000 and the cost of a bad hire is USD 50,000:
- \(\text{Extra FP Cost} = \Delta\text{FPR} \times \text{Bad Hire Cost}\) for applicants in the disadvantaged group.
- \(\text{Aggregate Utility Tax} = \frac{\text{Extra FP Cost}}{\text{Baseline Successful-Hire Utility} + \text{Extra FP Cost}} \times \text{Group Share}\).
- Under the assumption that the disadvantaged group is 30 percent of the applicant pool and that the base rate of qualified applicants is 50 percent, the aggregate utility loss is 1.4 percent.
Systems insight: The “Price of Fairness” in this system is a 1.4 percent utility tax under the stated assumptions, a System Constraint, not a bug. The exact figure depends on the base rate of qualified applicants and the disadvantaged group’s share of the pool; the engineer’s job is to present the Pareto frontier to stakeholders so they can choose the Utility/Fairness trade-off that aligns with organizational values.
Quantifying disparities through metrics is necessary but not sufficient for responsible deployment. When a loan applicant receives a rejection, stating that “the model’s true positive rate for your demographic group is 60 percent compared to 90 percent for other groups” provides no actionable information. The applicant needs to know why the application was rejected and what could be changed. These questions require explainability, which is the ability to articulate which input features drove specific predictions.
Explainability requirements
A loan applicant denied credit by an algorithmic system has a right to know why, not in aggregate statistical terms but in terms specific to her application. Explainability14 provides this capability: it enables human oversight of automated decisions, supports debugging when problems emerge, and satisfies regulatory requirements for decision transparency.
14 Explainability vs. Interpretability: Interpretability is an intrinsic model property—the degree to which a human can understand internal mechanics (linear regression is interpretable; a 100-layer network is not). Explainability is a post-hoc capability added without changing the model (LIME, SHAP). The systems implication: interpretable models constrain architecture selection (simpler models, fewer features), while explainability adds 10–100\(\times\) inference latency as a separate module. Regulations like the EU AI Act demand “meaningful information about the logic involved” without specifying which approach, leaving the latency-vs.-architecture trade-off to engineering teams.
The level of explainability required varies by application context and regulatory environment. Table 9 maps common deployment scenarios to their explainability needs.
| Application Domain | Explainability Level | Typical Requirements |
|---|---|---|
| Credit decisions | Individual explanation required | Specific factors contributing to denial must be disclosed to applicant |
| Medical diagnosis | Clinical reasoning support | Explanation must support physician decision-making, not replace it |
| Content moderation | Appeal-supporting | Sufficient detail for users to understand and contest decisions |
| Recommendation | Transparency optional | “Because you watched X” sufficient for most contexts |
| Fraud detection | Internal audit only | Detailed explanations may enable adversarial gaming |
Engineering teams should select explainability approaches based on these domain requirements. Post-hoc explanation methods (LIME, SHAP) generate feature importance scores for individual predictions without requiring model architecture changes.15 Inherently interpretable models (linear models, decision trees, attention mechanisms) provide explanations as part of their structure but may sacrifice predictive performance. Concept-based explanations map model behavior to human-understandable concepts rather than raw features. The choice involves trade-offs between explanation fidelity, computational cost, and model flexibility. Figure 4 arranges these trade-offs along a single axis. On the left side, decision trees and linear regression offer direct auditability: an engineer can inspect every coefficient or branching rule that produced a prediction, at the cost of limited representational capacity. On the right side, deep neural networks and convolutional architectures achieve higher accuracy on complex tasks but resist human inspection, requiring post-hoc tools like LIME or SHAP to approximate explanations. The choice depends on the application’s accountability requirements: high-stakes credit decisions subject to adverse action notice laws demand models near the interpretable end, while large-scale recommendation systems that face no per-decision regulatory scrutiny can tolerate opaque architectures. The spectrum does not imply “simple is always better,” because a highly interpretable model that makes wrong predictions serves no one. The engineering challenge is selecting the most interpretable model that meets accuracy requirements for the application.
15 LIME and SHAP: LIME (Ribeiro et al. 2016) fits a local interpretable model around each prediction—fast but potentially inconsistent across nearby inputs. SHAP (Lundberg and Lee 2017) adapts Shapley values from cooperative game theory to compute mathematically consistent feature contributions, but with exponential worst-case complexity. The systems trade-off is stark: SHAP adds 10–100\(\times\) inference latency, making LIME the only viable option for real-time serving where explanation must arrive within the same latency budget as the prediction itself.
War Story 1.4: The Clever Hans effect
The failure: When tested on data from other hospitals, performance collapsed. Heatmap analysis revealed the model was not looking at the lungs. Instead, it had learned to detect a metal token that technicians at the training hospital placed on the patient’s shoulder.
The consequence: The model was effectively a “metal token detector,” not a pneumonia detector. It had learned a spurious correlation that was 100 percent predictive in the training distribution but irrelevant to the medical pathology.
The systems lesson: Neural networks are lazy optimizers. They will exploit the easiest statistical signal to minimize loss, even if that signal is medically irrelevant. Interpretability tools (saliency maps) are not optional; they are quality assurance gates (Lapuschkin et al. 2019).
The explainability requirements outlined earlier carry the force of law, not merely of engineering best practice. The EU AI Act, which entered into force on August 1, 2024 and applies in phases, imposes documentation, transparency, human-oversight, and risk-management obligations for high-risk systems. US regulators also require adverse action notices in lending contexts, including when algorithmic tools contribute to credit decisions. Regulations transform explainability from a design choice into a compliance requirement with concrete penalties for failure, making the technical mechanisms just described prerequisites for legal operation.
The regulatory landscape
The EU AI Act entered into force on August 1, 2024 and applies in phases: prohibited-practice rules began applying in 2025, while high-risk and other operator obligations phase in by system category and implementation guidance. Article 99 sets maximum fines of EUR 35 million or 7 percent of global turnover for prohibited AI practices, while many other operator obligations are capped at EUR 15 million or 3 percent. In parallel, US regulators have brought enforcement actions involving algorithmic discrimination. Responsible engineering now operates within explicit regulatory frameworks that mandate specific technical requirements for transparency, oversight, and accountability. While regulations vary by jurisdiction, several convergent patterns have emerged that engineers must understand.
The EU AI Act
The EU AI Act establishes the most comprehensive framework to date, classifying AI systems by risk level and mandating requirements accordingly.16 High-risk systems17 (including those used in employment, credit, education, and critical infrastructure) must implement risk management systems, data governance practices, technical documentation, transparency measures, human oversight mechanisms, and accuracy/robustness/security requirements. The engineering implications are concrete: systems must be designed for auditability from inception, with documentation practices that demonstrate compliance.
16 EU AI Act (Regulation 2024/1689): The first comprehensive AI legal framework, defining four risk tiers with penalties that vary by infringement category. Prohibited AI-practice violations can reach EUR 35 million or 7 percent of global turnover; many other obligations, including many high-risk operator obligations, are capped at EUR 15 million or 3 percent. The Act has extraterritorial reach: non-EU organizations may need to comply when they place systems on the EU market or when system outputs are used in the EU. Systems engineering implications are concrete: high-risk AI requires logging infrastructure for audit trails, human oversight mechanisms built into the architecture, and CE marking—all capabilities that must be designed in from inception, not retrofitted after deployment.
17 High-Risk AI (EU AI Act Annex III): Risk classification is not subjective—Annex III enumerates eight specific domains: biometric identification, critical infrastructure, education and vocational training, employment and worker management, essential services access (credit, insurance), law enforcement, migration and border control, and justice administration. A system falls under high-risk requirements based on deployment context, not model architecture: a logistic regression approving loans faces the same compliance burden as a transformer, because the Act regulates what decisions are made, not how they are computed.
GDPR’s article 22
GDPR Article 22 grants EU data subjects the right not to be subject to decisions based solely on automated processing that produce legal or similarly significant effects, subject to specified exceptions and safeguards.18 GDPR Article 15(1)(h) separately gives data subjects access to meaningful information about the logic involved in automated decision-making referred to in Article 22. While legal interpretation varies, engineering teams should assume that every high-stakes automated decision requires both a human review mechanism where required and an explainability capability.
18 GDPR (General Data Protection Regulation) Articles 15 and 22: Article 22 restricts certain solely automated decisions with legal or similarly significant effects and, for specified exceptions, requires safeguards including human intervention, the ability to express a point of view, and the ability to contest the decision. Article 15(1)(h) contains the access right to meaningful information about the logic involved in such automated decision-making. The European Data Protection Board’s guidance emphasizes that required human oversight must be substantive and not merely a “rubber-stamping” exercise. A system making 1 million daily decisions with a 0.1 percent error rate requiring substantive review would generate 1,000 cases per day, an operational load that is untenable without built-in summarization and audit tools.
US sectoral regulations
US sectoral regulations impose domain-specific requirements that, while less unified than the EU AI Act, collectively create significant compliance obligations for ML systems. Fair lending laws (ECOA, Fair Housing Act) require creditors to provide specific reasons for adverse credit decisions—the origin of the “adverse action notice” requirement that drives explainability needs in financial ML. Healthcare regulations, including the Health Insurance Portability and Accountability Act (HIPAA)19 and FDA guidance, layer data protection and validation requirements onto medical AI systems, while employment law prohibits discriminatory hiring practices regardless of whether discrimination results from human or algorithmic decision-making. The cumulative effect is that any ML system operating across multiple domains faces an intersection of regulatory requirements, each mandating different technical capabilities.
19 HIPAA (Health Insurance Portability and Accountability Act): Enacted 1996, with Privacy Rule (2003) and Security Rule (2005) establishing standards for protected health information. ML-specific constraints are stringent: training data containing PHI must be de-identified, model outputs that could re-identify patients may constitute PHI themselves, and audit logs must be retained for six years. Penalties reach $50,000 per violation with $1.5 million annual maximums per category—sufficient to make a single poorly governed ML pipeline an existential financial risk for a healthcare startup.
The engineering response to these regulatory requirements is proactive architectural design. Teams that build documentation, monitoring, explainability, and human oversight into systems from inception demonstrate compliance efficiently. Teams that must retrofit these capabilities face expensive redesign or deployment constraints. The foundation established here, that responsibility is an engineering requirement rather than a legal afterthought, enables more targeted compliance strategies as regulatory frameworks mature. Yet even well-designed systems can fail, making incident response preparation essential.
Checkpoint 1.3: Ethical deployment
Deployment is the point of no return.
The Safety Net
The Monitoring Plan
Monitoring and incident response
Zillow reported a USD 304 million20 Q3 2021 Homes-segment inventory write-down after buying homes at prices above revised estimates of future selling prices. A systems diagnosis can interpret the failure as a combination of forecasting uncertainty, distribution shift, operational capacity limits, and insufficient circuit breakers. Planning for system failures before they occur is a core responsible engineering practice. Building on the incident severity classification and response framework from Incident response for ML systems, Table 10 extends the general framework with fairness-specific detection and response criteria, structuring preparation into five components with both requirements and predeployment verification criteria.
20 Zillow’s D·A·M Failure: Zillow’s USD 304M write-down in 2021 is a useful systems case because the documented business failure combined forecast uncertainty with operational execution. A D·A·M diagnosis interprets the Data axis as the mismatch between historical home-sale data and pandemic-era price volatility, the Algorithm axis as the difficulty of pricing homes with reliable uncertainty estimates, and the Machine axis as an automated iBuying pipeline that needed stronger capacity limits and circuit breakers. This is an engineering interpretation of Zillow’s public disclosure, not a claim that Zillow identified one root technical cause.
| Component | Requirements | Predeployment Verification |
|---|---|---|
| Detection | Monitoring systems that identify anomalies, degraded performance, and fairness violations | Alert thresholds tested, on-call rotation established, escalation paths documented |
| Assessment | Procedures for evaluating incident scope and severity | Severity classification defined, impact assessment templates prepared |
| Mitigation | Technical capabilities to reduce harm while investigation proceeds | Rollback procedures tested, fallback systems operational, kill switches functional |
| Communication | Protocols for stakeholder notification | Contact lists current, message templates prepared, approval chains defined |
| Remediation | Processes for permanent fixes and system improvements | Root cause analysis procedures, change management integration |
ML systems create unique maintenance challenges (Sculley et al. 2015). Models degrade silently, dependencies shift unexpectedly, and feedback loops amplify small problems into large ones. Incident response planning must account for these ML-specific failure modes, and effective response depends on continuous monitoring infrastructure that detects problems in the first place.
The monitoring infrastructure from ML Operations provides the foundation for responsible system operation, extending traditional operational metrics to include outcome quality measures.
Responsible monitoring extends along several interconnected dimensions. Performance stability tracking detects gradual prediction quality degradation that might not trigger immediate alerts. Slow accuracy decay that accumulates over weeks is far more dangerous than a sudden crash because it evades threshold-based alarms. Subgroup parity monitoring adds a fairness lens to this temporal tracking, comparing error rates across demographic groups to detect emerging disparities before they cause significant harm. These model-level metrics must be complemented by input distribution monitoring that catches population shifts and potential adversarial manipulation at the data layer, and by outcome monitoring that validates whether predictions translate to intended real-world results. User feedback systems close the loop by surfacing complaints and corrections that reveal problems invisible to any automated metric—the kind of harm that only affected users can articulate.
Effective monitoring requires both data collection infrastructure and disciplined review processes. Dashboards that no one examines provide no protection, so engineering teams must establish regular review cadences with clear ownership and escalation procedures.
The frameworks established in this section address one dimension of responsible engineering: ensuring systems work fairly and reliably across user populations. Fairness is not the only cost that conventional engineering metrics overlook. Every model training run, every inference request, every monitoring dashboard consumes electricity that translates into carbon emissions and dollar costs. A system can be perfectly fair across demographic groups while consuming orders of magnitude more resources than the task requires, harming not specific user populations but the broader environment and the organizations paying the bills. Responsible engineering must therefore extend beyond who the system serves to encompass what it costs to serve them.
Self-Check: Question
A team needs a statistically valid test set of 10,000 face images for a subgroup that makes up 1 percent of the user base to detect a one-percent performance gap with 95 percent confidence. Using the section’s representation statistics, what total sample collection does random sampling require, and what does this imply for the fairness evaluation workflow?
- About 100,000 total images, because confidence intervals shrink roughly linearly with the combined dataset size regardless of subgroup prevalence.
- About 1,000,000 total images, because subgroup confidence depends on subgroup sample count, so random collection requires a 100x multiplier relative to the target and makes intentional stratified collection an engineering prerequisite.
- About 10,000 total images, because the target test-set size is already fixed and subgroup composition is handled automatically by the model’s training procedure.
- Sample-size reasoning applies only to training data; evaluation confidence scales with the number of gradient-update steps, not with the subgroup sample count.
A team argues they will write their model card after launch so it can accurately reflect observed behavior. Explain why the section calls this a guard-rail failure, and describe one specific scope-creep scenario that a predeployment model card would have blocked but a post-launch card would not.
In the loan-approval worked example, Group A (majority) has a true positive rate of 90 percent and Group B (minority) has a true positive rate of 60 percent, while both groups share the same false positive rate of 20 percent. Evaluating each fairness criterion against these numbers, which statement is correct?
- Demographic parity is satisfied because the false positive rates match across groups.
- Equal opportunity is violated by the 30-point true-positive-rate gap, and equalized odds is also violated because equalized odds requires both true-positive-rate and false-positive-rate equality, so matching false positive rates alone is not sufficient.
- Equalized odds is satisfied because one of its two component rates matches across groups.
- Only calibration is implicated, because true-positive-rate disparities affect model accuracy rather than fairness.
Stakeholders ask a hiring team to close a 20-percentage-point true-positive-rate gap between two groups by lowering the decision threshold for the disadvantaged group. Using the Pareto-frontier framing and the price-of-fairness calculation from the section, analyze what the team should present to stakeholders and why threshold adjustment alone is a design choice, not a technical fix.
A European lender plans to deploy a deep neural network that automates credit decisions affecting hundreds of thousands of applicants per year. Given EU AI Act high-risk classification and GDPR Article 22 obligations as described in the section, which architectural consequence follows most directly?
- Because deeper models are more accurate, explainability engineering can be deferred until after legal approval closes.
- Aggregate fairness metrics alone are sufficient because individual applicant explanations are irrelevant in financial decisions.
- The deployment architecture must be designed at inception to support per-applicant explanations, substantive human review of automated decisions, and audit-trail logging, because adverse-action and Article 22 substantive-review obligations are enforced as technical requirements with 35M EUR or 7-percent-global-turnover penalties.
- EU regulation applies primarily to foundation models, so a loan classifier with fewer than a billion parameters can be deployed without explainability infrastructure.
Environmental and Cost Awareness
In 2019, researchers estimated that training a single large NLP model emitted as much carbon as five cars over their entire lifetimes (Strubell et al. 2019), a finding that sparked the “Green AI” movement and forced the field to confront the full cost of ML systems. Training runs consume megawatt-hours of electricity, inference at scale multiplies per-request inefficiencies into measurable environmental impact, and resource-intensive models exclude organizations that lack large compute budgets. The optimization techniques introduced in earlier chapters therefore serve double duty as instruments of responsible engineering, connecting computational efficiency to environmental sustainability, economic accessibility, and long-term scalability.
Efficiency as responsibility
Training a single large language model consumes thousands of GPU hours and energy measured in megawatt-hours. Much of this expense, however, is not intrinsic to the learning task but represents accidental complexity: training from scratch when fine-tuning would suffice, using larger models than tasks require, and running hyperparameter searches that explore redundant configurations. Computational cost is largely a function of engineering discipline, not just model physics.21
21 Green AI: Schwartz et al. (2020) contrasted “Red AI” (performance at any cost) with “Green AI” (efficiency as primary metric), documenting that state-of-the-art accuracy gains from 2012–2018 required a 300,000\(\times\) compute increase. Their proposal—reporting FLOPs alongside accuracy for every published result—reframes efficiency from an engineering preference into a scientific reporting obligation, making the resource cost of marginal accuracy gains visible and comparable across research groups.
Resource efficiency and responsible engineering are directly linked through three interconnected channels. The most direct connection is environmental: a model that requires 4\(\times\) more compute than necessary generates 4\(\times\) more carbon emissions, so the efficiency techniques from Model Compression that enable edge deployment also reduce the environmental footprint of cloud inference. Efficiency also drives accessibility, because resource-efficient models can run on less expensive hardware, democratizing access to ML capabilities. A quantized model that runs on a smartphone enables users who cannot afford cloud API costs. Finally, sustainability at scale amplifies both effects: systems serving millions of users multiply inefficiencies across every request, so a 10 ms latency reduction per query translates to thousands of GPU-hours saved annually.
The techniques from earlier chapters directly serve responsibility goals. Quantization (Model Compression) reduces compute by 2–4\(\times\) with minimal accuracy impact. Pruning removes 50–90 percent of parameters. Knowledge distillation typically achieves 5–20\(\times\) compression while retaining 90–95 percent of the original accuracy. Hardware acceleration (Hardware Acceleration) achieves 10–100\(\times\) better energy efficiency than general-purpose processors.
Responsible engineers apply these techniques as design requirements, not afterthoughts. The question shifts from maximizing accuracy alone to maximizing accuracy within efficiency constraints.
Efficiency engineering in practice
Acknowledging that efficiency matters is the easy part; the harder engineering challenge is translating that principle into measurable targets. The goal is selecting the smallest model that meets task requirements, then applying methodical optimization to reduce resource consumption further. Edge deployment scenarios make these constraints concrete because they impose hard physical limits that cannot be negotiated away.
Edge deployment scenarios make efficiency requirements concrete. When a wearable device has a 500 mW power budget and must run inference continuously for 24 hours on a small battery, abstract efficiency discussions become engineering constraints with measurable consequences. Table 11 quantifies these constraints across four deployment contexts, from smartphones with 5 W budgets to IoT sensors operating at 100 mW.
| Deployment Context | Power Budget | Latency Requirement | Typical Use Cases |
|---|---|---|---|
| Smartphone | 5 W | 100 ms | Photo enhancement, voice assistants |
| IoT Sensor | 100 mW | 1 second | Anomaly detection, environmental monitoring |
| Embedded Camera | 1 W | 30 FPS (33 ms) | Real-time object detection, surveillance |
| Wearable Device | 500 mW | 500 ms | Health monitoring, activity recognition |
Table 12 compares how model architectures fit different deployment constraints.
The benchmarks in Table 12 provide actionable guidance for efficiency optimization. Techniques that enable deployment on power-constrained platforms (quantization, pruning, and efficient architectures) directly reduce environmental impact per inference regardless of deployment context. Power savings at inference time translate directly to financial savings when aggregated across millions of requests.
| Model | Parameters | Inference Power | Latency | Fits Smartphone? | Fits IoT? |
|---|---|---|---|---|---|
| MobileNetV2 | 3.5 M | 1.2 W | 40 ms | Yes | No |
| EfficientNet-B0 | 5.3 M | 1.8 W | 65 ms | Yes | No |
| ResNet-50 | 25.6 M | 4.5 W | 180 ms | No | No |
| TinyML Model | 200 K | 50 mW | 200 ms | No | Yes |
For the wearable budget in Table 11, the TinyML model leaves a 10\(\times\) power margin, while MobileNetV2 exceeds the same power budget by 2.4\(\times\) before accounting for sustained thermals.
Total cost of ownership
A team spends USD 3,200 training a recommendation model and celebrates the modest cost. Six months later, they discover they are spending USD 500,000 per year serving it. The surprise exposes a structural asymmetry in total cost of ownership22: power budgets translate directly to financial costs (a model that consumes 2 W instead of 4 W cuts electricity expenses in half), and for successful production systems, inference costs typically exceed training costs by ten to 1,000 times depending on traffic volume. Inference cost dominance dictates where optimization efforts should focus.
22 Total Cost of Ownership (TCO): The standard TCO figure typically excludes three categories of costs that ML systems add over conventional software: data labeling infrastructure (often 10–30 percent of total ML project cost), model monitoring and retraining (ongoing operational cost proportional to data volume), and remediation costs when models fail (which in regulated industries can exceed the original development cost). Additional externalities (carbon emissions, fairness audits, regulatory compliance overhead) make the upfront compute cost a misleading proxy for ML system cost, and explain why inference dominates TCO by 10–1,000\(\times\) over training for any system that reaches production scale.
Consider a concrete example of a recommendation system serving 10 million users daily. Training costs appear considerable: data preparation consumes 100 GPU-hours at approximately USD 4 per hour (USD 400), hyperparameter search across multiple configurations requires 500 GPU-hours (USD 2,000), and the final training run uses 200 GPU-hours (USD 800). Total training cost reaches approximately USD 3,200.
Inference costs dominate. With 10 million users each receiving 20 recommendations per day, the system serves 200 million inferences daily. Assuming 10 milliseconds per inference on GPU hardware, the system requires approximately 23 GPUs running continuously. At USD 2.50 per GPU-hour, annual GPU costs reach USD 506,944.
Over a three-year operational period, quarterly retraining produces total training costs of approximately USD 38,400, while inference costs over the same period total USD 1.5 million. The 40:1 ratio between inference and training costs is typical for production systems, directing optimization effort toward inference latency and serving efficiency rather than training speed.
Per-query optimization becomes essential when serving billions of requests. Reducing inference latency by ten milliseconds per query translates to measurable reductions in required hardware across billions of queries despite appearing negligible for individual requests. Hardware selection between CPU, GPU, and Tensor Processing Unit (TPU) deployment changes costs and carbon footprint by factors of ten or more. Model compression through quantization and pruning delivers immediate return on investment for high-volume systems because inference cost reduction compounds across every subsequent query.
Total cost of ownership encompasses additional dimensions beyond computation. Operational costs include monitoring, maintenance, retraining, and incident response, all of which scale with system complexity and the rate of distribution shift in the application domain. Opportunity costs reflect that resources consumed by ML systems cannot be used for other purposes. Wasteful resource consumption in one project constrains what other projects can attempt.
Engineers should evaluate whether the value an ML system delivers justifies its resource consumption. A recommendation system that increases engagement by 1 percent might not justify millions of dollars in computational costs, while a medical diagnosis system that saves lives does. Explicit trade-offs enable responsible resource allocation.23
23 ML Return on Investment: The 10:1 deployment-to-training cost ratio emerges from the composition of monitoring (continuous), retraining (periodic), infrastructure (ongoing), and incident response (unpredictable), each of which scales with deployment duration and data volume rather than with the initial development effort. A model deployed for three years accumulates roughly 10–15\(\times\) its development cost in operational overhead. Responsible engineering practices that reduce incident frequency and severity therefore yield ROI proportional to deployment lifetime, explaining why a logistic regression at 1 percent of the cost often represents the correct engineering decision when the TCO difference compounds over years.
Quantifying environmental impact requires converting compute hours into carbon emissions, making carbon a first-class engineering metric alongside dollar cost.
TCO calculation methodology
Engineers can estimate three-year total cost of ownership using a structured approach that accounts for training, inference, and operational costs. The following methodology applies to the recommendation system example discussed earlier.
Systems Perspective 1.4: The carbon cost of compute
For the following TCO examples, we use these baseline assumptions:
- Power: 400 W per GPU-hour (scenario baseline).
- Intensity: 0.4 kg CO2eq/kWh (rounded grid baseline).
- Conversion factor: (0.4 kW \(\times\) 1 hour) \(\times\) 0.4 kg/kWh = 0.16 kg CO2eq per GPU-hour.
The conversion factor allows us to track “Carbon Cost” alongside “Dollar Cost” in our ledgers.
Training costs
Training costs include both initial development and ongoing retraining. Table 13 breaks down these costs, showing how quarterly retraining cycles accumulate over a three-year operational period.
| Cost Component | Calculation | Financial Cost | Carbon (kg CO2) |
|---|---|---|---|
| Initial data preparation | hours \(\times\) rate | 100 GPU-hr × $4 = $400 | 16 kg |
| Hyperparameter search | experiments \(\times\) cost/experiment | 50 × $40 = $2,000 | 80 kg |
| Final training | hours \(\times\) rate | 200 GPU-hr × $4 = $800 | 32 kg |
| Subtotal per training cycle | 3,200 | 128 kg | |
| Retraining frequency | cycles/year \(\times\) years | 4/year × 3 years = 12 | same multiplier (12 cycles) |
| Total training cost | subtotal \(\times\) cycles | 38,400 | 1,536 kg |
Inference costs
The economics of this trade-off are detailed in Table 14, which shows how inference costs dominate total cost of ownership for production systems.
| Cost Component | Calculation | Financial Cost | Carbon (kg CO2) |
|---|---|---|---|
| Daily queries | users \(\times\) queries/user | 10M × 20 = 200M | - |
| GPU-seconds/day | queries \(\times\) latency | 200M × 0.01 s = 2.0M sec | - |
| GPU-hours/day | seconds ÷ SEC_PER_HOUR | 556 GPU-hr | 89 kg |
| Annual GPU cost | hours \(\times\) 365 \(\times\) rate | 556 × 365 × $2.50 = $507K | 32,444 kg |
| 3-year inference cost | annual \(\times\) 3 | $1.52M | 97,333 kg |
Operational costs
Operational costs encompass infrastructure, personnel, and incident response. Table 15 itemizes these ongoing expenses, which often surprise teams focused primarily on compute costs.
| Cost Component | Annual Estimate | 3-Year Total |
|---|---|---|
| Monitoring infrastructure | $50K | $150K |
| On-call engineering (0.5 FTE) | $100K | $300K |
| Incident response (estimated) | $20K | $60K |
| Total operational | $510K |
The stark breakdown in Table 16 answers where the money goes: inference at 73 percent, operations at 25 percent, and training at only 2 percent.
| Category | 3-Year Cost | Percentage | Carbon Impact |
|---|---|---|---|
| Training | $38K | 2% | 1.5 tons |
| Inference | $1.52M | 73% | 97.3 tons |
| Operations | $510K | 25% | - |
| Total TCO | $2.07M | 100% | ~99 tons |
Those proportions turn efficiency from a tuning preference into a responsibility check.
Checkpoint 1.4: Efficiency as responsibility
Total cost of ownership reveals where responsible optimization has the most leverage.
Environmental impact
The preceding TCO analysis captures costs that appear on invoices, but computational resources carry costs that no invoice reflects. Environmental impact follows from computational efficiency: the same optimization techniques that reduce TCO also reduce carbon emissions. The optimization techniques from Hardware Acceleration and Model Compression reduce energy consumption per inference, directly lowering carbon footprint. Data centers consume an estimated 1–2 percent of global electricity, a share that continues to grow as ML workloads expand (Henderson et al. 2020). Engineers can reduce this impact by selecting cloud regions powered by renewable energy (5\(\times\) carbon reduction), applying model efficiency techniques (2–4\(\times\) reduction through quantization), and scheduling intensive workloads during periods of abundant renewable energy.
The magnitude becomes clearer in a scale calculation for training a large foundation model.
Napkin Math 1.4: The carbon cost of scale
Math:
- Energy consumption: 1,287 MWh = 1,287,000 kWh.
- Carbon intensity: The average US grid emits \(\approx\) 429 g CO2 per kWh (0.429 kg/kWh).
- Total emissions: 1,287,000 \(\times\) 0.429 = 552,123 kg CO2 (552 metric tons).
- Comparison: A typical passenger car emits ≈ 4.6 metric tons of CO2 per year.
Systems insight: Training a single state-of-the-art model is equivalent to the annual carbon footprint of 120 cars. At this scale, efficiency transforms from a technical preference into a moral requirement. Every 1 percent improvement in the Efficiency \((\eta_{\text{hw}})\) of a training pipeline removes the equivalent of about 1.2 cars’ annual emissions from the atmosphere.
The key insight is that efficiency optimization and environmental responsibility align: the techniques that reduce inference costs also reduce carbon emissions per prediction. More granular carbon accounting methodologies—lifecycle assessment, scope 1/2/3 emissions tracking, and carbon-aware scheduling—build on this foundation for organizations requiring detailed environmental impact analysis.
The same physical invariants that govern performance also govern responsibility. The energy-movement invariant determines both chip-level computational efficiency and data-center-level carbon footprints. The physics is identical; only the unit of cost changes from joules per inference to tons of CO2 per year. The Pareto frontier governs accuracy-fairness trade-offs with the same mathematical force as accuracy-latency trade-offs: improving one metric without sacrificing another requires moving to a strictly superior architecture, not reweighting an objective. Responsible engineering is the same constrained optimization problem this book has been teaching, evaluated over a wider set of objectives that include societal impact alongside throughput and latency.
The checklists, fairness metrics, explainability mechanisms, and efficiency analyses developed in previous sections tell engineering teams what to measure and how to act. A natural follow-up concern is what infrastructure ensures that answers are recorded, costs are audited, and violations trigger automated intervention rather than relying on human vigilance. The answer lies in data governance—the engineering discipline that transforms policy intentions into enforceable technical controls.
Self-Check: Question
A team can deploy either a full-precision model or a quantized version that preserves task accuracy while cutting inference compute by roughly 4x. According to the section, why does this efficiency choice count as a responsibility decision rather than purely a performance decision?
- Quantization is primarily a responsibility tool because it automatically reduces fairness disparities by making all user groups equally cheap to serve.
- Quantization reduces compute per inference, which simultaneously shrinks carbon emissions in proportion, lowers serving dollar cost, and lowers hardware barriers so smaller organizations and edge devices can deploy the model.
- Quantization is a pure performance optimization that should be evaluated separately from responsibility, because fairness, carbon, and cost belong to distinct engineering layers with different owners.
- Quantization matters mainly for training-time energy: production inference is usually a minor fraction of lifecycle resource use, so the responsibility payoff is small.
A wearable device has a 500 mW sustained power budget and a 500 ms end-to-end inference latency requirement. Using the section’s deployment-comparison data (TinyML at roughly 50 mW / 200 ms, MobileNetV2 at roughly 1.2 W / 40 ms, EfficientNet-B0 at roughly 1.8 W, ResNet-50 much larger), which model selection is the correct responsible-engineering choice, and why?
- ResNet-50, because larger models achieve better energy efficiency per accuracy point once their throughput is amortized through batching.
- MobileNetV2, because 1.2 W is close enough to the 500 mW target that the gap is operationally negligible on modern battery-management hardware.
- TinyML model, because its 50 mW power draw fits 10x under the budget and its 200 ms latency fits under the 500 ms requirement, so it is the only option that satisfies both constraints simultaneously.
- EfficientNet-B0, because its smartphone-grade footprint guarantees it also fits wearable constraints once the form factor is reduced.
Using the section’s three-year TCO breakdown (training ~2 percent, inference ~73 percent, operations ~25 percent for a recommendation system serving 200M daily queries), a team proposes two optimization options: Proposal 1 is a 50 percent reduction in training wall-clock time, and Proposal 2 is a 20 percent reduction in per-query inference latency via quantization. Explain which proposal has higher leverage on both dollar cost and carbon, and give the rough dollar-savings ratio between them.
True or False: For an identical model and serving workload, migrating deployment from a carbon-intensive cloud region to one powered by abundant renewable energy can reduce inference emissions more than a one-time modest algorithmic efficiency improvement.
Training GPT-3 consumed roughly 1,287 MWh of electricity. At a US-grid average carbon intensity of roughly 0.429 kg CO2 per kWh, what does the section identify as the dominant responsible-engineering lever for reducing the footprint of future foundation-model training runs?
- Reducing model size to under one billion parameters, accepting the corresponding accuracy loss, because parameter count is the only significant driver of training energy.
- Improving accelerator utilization η during training so that the same 1,287 MWh produces more useful FLOPs, combined with carbon-aware scheduling that runs intensive jobs when renewable supply is abundant and selecting regions with lower grid-carbon intensity.
- Deferring all training until grid carbon intensity reaches zero, since any non-zero intensity produces emissions that cannot be justified ethically.
- Switching the entire training pipeline from FP32 to FP16 without other changes, because numerical precision alone accounts for the bulk of training energy use.
Data Governance and Compliance
In January 2023, the Irish Data Protection Commission issued separate EUR 210 million and EUR 180 million fines (totaling EUR 390 million) against Meta Ireland for relying on contractual necessity as the legal basis for personalized advertising on Facebook and Instagram—penalties that stemmed not from a data breach but from insufficient governance infrastructure to demonstrate lawful processing. The storage architectures examined in Data Engineering are governance enforcement mechanisms that determine who accesses data, how usage is tracked, and whether systems comply with regulatory requirements. Every architectural decision, from acquisition strategies through processing pipelines to storage design, carries governance implications that manifest when systems face regulatory audits, privacy violations, or ethical challenges. Data governance transforms from abstract policy into concrete engineering: access control systems that enforce who can read training data, audit infrastructure that tracks every data access for compliance, privacy-preserving techniques that protect individuals while enabling model training, and lineage systems that document how raw audio recordings become production models.
Data governance encompasses four interconnected domains. Security infrastructure protects data assets through access control and encryption, establishing the perimeter within which all other governance operates. Privacy mechanisms then determine what information is exposed even to authorized users, respecting individual rights while enabling model training. Compliance frameworks translate jurisdiction-specific regulatory requirements into architectural constraints that shape how data flows through the system. Finally, lineage and audit systems create the accountability trails that make the first three domains verifiable—without them, security policies, privacy guarantees, and compliance claims are unenforceable assertions rather than demonstrable properties. The starting point is a critical constraint: compliance is not optional.
Data governance is not optional. The EU General Data Protection Regulation (GDPR) imposes fines up to 4 percent of global annual revenue or EUR 20 million (whichever is greater) for noncompliance. GDPR mandates specific technical capabilities: the right to erasure (Article 17) requires systems that can locate and delete all data associated with an individual, including derived features and model artifacts. GDPR Articles 15 and 22 together create engineering needs for automated-decision systems: access to meaningful information about automated decision logic, mechanisms for human intervention where required, and the ability to contest qualifying decisions. California’s CCPA, Brazil’s LGPD, and China’s PIPL impose similar obligations with jurisdiction-specific requirements. For ML systems, these are not legal abstractions but engineering specifications that must be built into data pipelines, storage architectures, and model training workflows from the outset.
The Lighthouse KWS system, the keyword-spotting voice assistant introduced in ML Systems and used as a running example throughout earlier chapters, illustrates how the fairness risks identified in Table 5 intensify at the governance level. Always-listening devices continuously process audio in users’ homes, feature stores maintain voice pattern histories across millions of users, and edge storage caches models derived from population-wide training data. These capabilities create governance obligations around consent management, data minimization, access auditing, and deletion rights.
These governance obligations can be summarized as four operational pillars, each with distinct engineering mechanisms. Privacy protects individuals through techniques like differential privacy and data minimization, limiting what the system retains beyond its immediate training purpose. Security prevents unauthorized access through encryption at rest and in transit, role-based access controls, and audit logging of every query against the feature store. Compliance ensures adherence to regulatory frameworks such as GDPR and CCPA, translating legal requirements into concrete system capabilities like erasure pipelines and consent management APIs. Transparency enables accountability through documentation of data provenance, model lineage, and decision audit trails. Figure 5 shows the broader operating model that supports these obligations: organization, policies, data catalogs, data sourcing, data quality, data operations, data security, and shared definitions. The four obligations and the operating model must work together because a failure in any one undermines the others: encrypted data with no access controls is still vulnerable, and compliant storage without transparency cannot survive a regulatory audit. In the context of the D·A·M taxonomy, governance provides the structural integrity for the Data axis, ensuring that the fuel for our systems remains safe, compliant, and reliable across the entire data lifecycle.
Security and access control architecture
Consider a data scientist querying a feature store for training data. She can read aggregated voice features but cannot access the raw audio recordings from which they were derived. The serving pipeline can read online features for inference but cannot write to the training dataset. Neither can modify source data. The separation is intentional: it reflects a layered security architecture where governance requirements translate into enforceable technical controls at each pipeline stage. Modern feature stores implement role-based access control (RBAC) that maps organizational policies into database permissions, preventing unauthorized access. These controls operate across storage tiers: object storage like S3 enforces bucket policies, data warehouses implement column-level security that hides sensitive fields, and feature stores maintain separate read/write paths with different permission requirements.
Access control mechanisms remain incomplete without encryption, which protects data throughout its lifecycle even when access controls are bypassed or misconfigured. Training data stored in data lakes uses server-side encryption with keys managed through dedicated key management services (AWS KMS, Google Cloud KMS) that enforce separation. Feature stores implement encryption both at rest (storage encrypted using platform-managed keys) and in transit (TLS 1.3 for all communication). For Lighthouse KWS edge devices, model updates require end-to-end encryption and code signing that verifies model integrity, preventing adversarial model injection that could compromise device security or user privacy.
Access control and encryption establish who can reach data and how it is protected in transit and at rest. Controlling access is only half the problem: even authorized users can compromise individual privacy if the data itself is insufficiently protected.
Technical privacy protection methods
A data scientist with legitimate access to training data does not need, and should not see, individual user records when aggregate statistics suffice. Privacy-preserving techniques24 address this gap by determining what information systems expose even to authorized users, adding a second layer of protection beyond access control. Differential privacy provides formal mathematical guarantees that individual training examples do not leak through model behavior. Implementing differential privacy in production requires careful engineering: adding calibrated noise during model development, tracking privacy budgets across all data uses, and validating that deployed models satisfy privacy guarantees through testing infrastructure that attempts to extract training data through membership inference attacks.25
24 Privacy-Preserving Techniques: Before differential privacy, the field relied on syntactic guarantees: k-anonymity (Sweeney 2002) ensures each record is indistinguishable from \(k-1\) others, l-diversity adds attribute variety within equivalence classes, and t-closeness bounds distribution distance. All three fail against ML-specific attacks: a model trained on k-anonymized data can still memorize and leak individual records through membership inference. Differential privacy’s semantic guarantee (\(\epsilon\)-bounded influence per record) is the only approach proven robust against arbitrary adversaries, explaining why it displaced syntactic methods for ML training despite its higher utility cost.
25 Membership Inference Attack: The attack exploits a model’s higher prediction confidence on examples from its training set, a direct signal of overfitting. Membership inference provides the core validation method for the privacy engineering described: if an attacker can determine a specific record was used for training, the privacy guarantee is violated, even if the record’s content is not exposed. The attack’s success rate—which can exceed 90 percent on overfit models—serves as the standard benchmark for quantifying this information leakage.
26 Federated Learning: From Latin foedus (treaty, covenant)—the name describes independent entities collaborating while retaining autonomy. McMahan et al. (2017) introduced Federated Averaging (FedAvg): each device trains locally and shares only gradient updates, never raw data. The etymology explains the design: federated learning provides “data minimization by architecture.” However, gradient updates can leak training data through reconstruction attacks, motivating the combination of federated learning with differential privacy—a defense-in-depth pattern where neither mechanism alone suffices.
KWS systems face particularly acute privacy challenges because the always-listening architecture requires processing audio continuously while minimizing data retention and exposure. Production systems implement privacy through three architectural choices. On-device processing ensures that wake word detection runs entirely locally, with audio never transmitted unless the wake word is detected. Federated learning26 allows devices to train on local audio and improve wake word detection while sharing only aggregated model updates, never raw recordings. Automatic deletion policies ensure that detected wake word audio is retained only briefly for quality monitoring before being permanently removed from storage. Data lakes implement lifecycle policies that automatically delete voice samples after 30 days unless explicitly tagged for long-term research use, and feature stores implement time-to-live (TTL) fields that cause user voice patterns to expire and be purged from online serving stores.
Architecting for regulatory compliance
When a European user invokes the “right to erasure” under GDPR, the voice assistant must locate and delete every recording, derived feature, and model artifact associated with that user across distributed storage systems, all within 30 days. The requirement is not a policy aspiration; it is an engineering specification with a deadline. Compliance requirements transform from legal obligations into system architecture constraints that shape pipeline design, storage choices, and operational procedures. GDPR’s data minimization principle requires limiting collection and retention to what is necessary for stated purposes. For KWS systems, this means justifying why voice samples need retention beyond training, documenting retention periods in system design documents, and implementing automated deletion once periods expire. The “right to access” requires systems to retrieve all data associated with a user, consolidating results from distributed storage systems.
Voice assistants operating globally face overlapping regulatory regimes because compliance requirements vary by jurisdiction and apply differently based on user age and data sensitivity. European requirements for cross-border data transfer restrict storing EU users’ voice data on servers outside designated countries unless specific safeguards exist, driving architectural decisions about regional data lakes, feature store replication strategies, and processing localization. Standardized documentation frameworks like data cards (Pushkarna et al. 2022) translate these compliance requirements into operational artifacts. Examine the data card template in Figure 6 to see how this structured format turns abstract compliance obligations into concrete, machine-checkable fields. Training pipelines check that input datasets have valid data cards before processing, and serving systems enforce that only models trained on compliant data can deploy to production.
Building data lineage infrastructure
Compliance obligations are only as credible as the infrastructure that demonstrates them. When a regulator asks “which training data produced this model?” or a user invokes their right to erasure, the organization must answer with engineering precision, not manual investigation. Data lineage provides this capability, transforming compliance documentation into operational infrastructure that powers governance across the ML lifecycle. Modern lineage systems like Apache Atlas and DataHub27 integrate with pipeline orchestrators (Airflow, Kubeflow) to automatically capture relationships: when an Airflow directed acyclic graph (DAG) reads audio files from S3 and transforms them into spectrograms, the lineage system records each step, creating a graph that traces any feature back to its source audio file. Automated tracking proves essential for deletion requests. When a user invokes GDPR rights, the lineage graph identifies all derived artifacts (extracted features, computed embeddings, trained model versions) that must be removed or retrained.
27 Data Lineage Systems: Apache Atlas and LinkedIn’s DataHub capture metadata about data flows automatically from pipeline execution logs, creating directed graphs where nodes are datasets and edges are transformations. GDPR Article 30 requires detailed records of all processing activities, making automated lineage tracking essential: when a user invokes the right to erasure, the lineage graph identifies every derived artifact—features, embeddings, trained models—that must be removed or retrained, a task that is infeasible manually at production scale.
Production KWS systems implement lineage tracking across all stages of the data engineering lifecycle. Source audio ingestion creates lineage records linking each audio file to its acquisition method, enabling verification of consent requirements. Processing pipeline execution extends lineage graphs as audio becomes features and embeddings, and each transformation adds nodes that record code versions and hyperparameters. Training jobs create lineage edges from feature collections to model artifacts, recording which data versions trained which model versions. When a voice assistant device downloads a model update, lineage tracking records the deployment, enabling recall if training data is later discovered to have quality or compliance issues.
Audit infrastructure and accountability
Lineage tracks what data exists and how it transforms through the pipeline. Governance also requires knowing who accessed data and when: the accountability dimension that lineage alone cannot provide. Audit systems record these access events, creating accountability trails required by regulations like HIPAA and SOX28. Production ML systems generate enormous audit volumes, necessitating specialized infrastructure: immutable append-only storage that prevents tampering with historical records, efficient indexing that enables querying specific user or dataset accesses, and automated analysis that detects anomalous patterns indicating potential security breaches or policy violations.
28 Audit Trail: The append-only requirement (audit entries can be added but never modified or deleted) forces write-once storage architectures, typically implemented as append-only columnar stores (Apache Iceberg, Delta Lake) or cryptographic hash chains. A large platform may log over 50 billion events daily; with HIPAA’s six-year retention mandate, storage cost grows monotonically with deployment lifetime. A model in production for five years accumulates audit records proportional to its prediction volume, making storage planning a first-class concern at deployment time—not an afterthought.
KWS systems implement multi-tier audit architectures that balance granularity against performance and cost. Edge devices log critical events locally with logs periodically uploaded to centralized storage for compliance retention. Feature stores log every query with request metadata: which service requested features, which user IDs were accessed, and what features were retrieved. Training infrastructure logs dataset access, recording which jobs read which data partitions, implementing the accountability needed to demonstrate that deleted user data no longer appears in new model versions.
Together, the four governance domains—security, privacy, compliance, and audit—form the enforcement layer that makes every other practice in this chapter durable. Data governance ensures that measurements are captured, actions are recorded, and commitments are verifiable under regulatory scrutiny. Without this infrastructure, responsible engineering remains aspirational; with it, responsibility becomes a demonstrable system property.
With the complete engineering toolkit now assembled—assessment frameworks, fairness metrics, explainability mechanisms, efficiency analyses, and governance infrastructure—one might expect responsible deployment to be straightforward. It is not. Teams armed with the right tools still fail to deploy responsible systems, often in predictable ways that stem from intuitions developed in traditional software engineering, where bugs are local and testing is deterministic. Recognizing these common failure patterns is essential because identifying a fallacy before it shapes a design decision is far cheaper than discovering it after deployment.
Self-Check: Question
In 2023 Meta received a 390M EUR fine not for a data breach but for insufficient governance infrastructure to demonstrate lawful processing. Which diagnosis best captures why the section frames data governance as an enforcement mechanism rather than a policy document?
- Governance replaces the need for model monitoring once regulators sign off on the data pipeline, because certification transfers ongoing responsibility to the certifier.
- Governance is primarily about publishing external-facing datasheets and model cards so that readers outside the organization can assess the system.
- Policy claims become demonstrable only when access controls, privacy mechanisms, lineage tracking, and audit logs make each requirement technically enforceable across the data lifecycle — otherwise compliance is an assertion rather than evidence.
- Governance applies only to raw storage, since derived features, model artifacts, and deployment workflows are downstream and fall outside the data lifecycle.
A European user of a voice-assistant service invokes GDPR Article 17 right-to-erasure. Explain why a manual search across storage systems is both unreliable and too slow to satisfy the request, and describe what automated infrastructure the compliance architecture must instead provide.
The Lighthouse KWS system is an always-listening keyword-spotting voice assistant deployed in users’ homes. Which architectural combination best reflects the section’s privacy-by-design approach for this deployment, and why?
- Stream all ambient audio to a cloud service that applies strong centralized privacy controls after collection, since centralized processing allows more sophisticated mechanisms than any edge device can run.
- Run wake-word detection on-device, transmit only aggregated or federated updates rather than raw recordings, and enforce automatic retention and deletion policies on any audio that must be retained, so the system minimizes the personal data exposed in the first place.
- Retain raw audio indefinitely on secure cloud storage, because the future retraining value of long-horizon voice data outweighs privacy concerns when access is properly encrypted.
- Rely on role-based access control as the sole privacy mechanism, since privacy concerns reduce to limiting who can query the data and RBAC solves exactly that problem.
A teammate argues that security, privacy, and audit are essentially the same concern because each restricts data access. Using the section’s governance stack, distinguish the operational role of each and give one concrete failure mode that would not be caught if the other two were fully implemented but that mechanism were missing.
True or False: Because GDPR Article 17 (right-to-erasure) penalties are capped at modest administrative amounts, an ML team can reasonably defer building automated lineage infrastructure until the first deletion request arrives.
Fallacies and Pitfalls
Fallacy: Responsibility can be addressed after the system achieves technical objectives.
Teams assume fairness constraints can be retrofitted once models demonstrate strong benchmark performance. In production, early architectural decisions constrain what interventions remain feasible. Amazon’s recruiting tool (see Section 1.2.1) illustrates this trap: remediation failed because the model had learned proxy signals, leading to project cancellation after considerable investment. Organizations deferring responsibility face expensive redesign (6–12 months of rework), deployment with documented risks, or cancellation. Integrating fairness constraints at system inception costs weeks; retrofitting costs quarters.
Pitfall: Relying on aggregate metrics to assess fairness.
Engineers assume high overall accuracy indicates the system works well for all users. The Flaw of Averages (Section 1.3.3) reveals this intuition fails: aggregate metrics conceal disparities exceeding 40\(\times\) between demographic groups (Section 1.2.4). The loan approval analysis in Section 1.3.3.1 showed a 30 percentage point TPR gap, meaning qualified minority applicants faced 4\(\times\) higher rejection rates. These disparities persist for months undetected because standard monitoring tracks only aggregates. Production systems require disaggregated evaluation with alerts when subgroup disparity exceeds 1.25\(\times\) error rate ratio or 5 percentage point TPR difference.
Fallacy: Removing sensitive attributes from training data eliminates bias.
Teams remove gender, race, and protected attributes expecting this ensures fairness. Models reconstruct protected attributes through proxy variables that correlate with sensitive characteristics. Research demonstrates that models recover protected attributes with 70–90 percent accuracy from supposedly neutral features like ZIP codes, purchase patterns, and browsing history. Amazon’s system (see Section 1.2.1) learned gender from college names and activity descriptions despite explicit removal. Healthcare algorithms excluded race but encoded unequal access through cost history; a population-health study found that correcting the bias would increase the share of Black patients receiving additional help from 17.7 percent to 46.5 percent. Feature removal without causal analysis creates false confidence while bias persists.
Pitfall: Treating documentation as sufficient accountability.
Teams invest effort in model cards, then consider responsibility requirements satisfied. Documentation provides transparency (Section 1.3.2) but not enforcement. Studies of model deployment patterns show 40–60 percent of production models operate outside their documented scope within 18 months. A model card specifying “not validated for high-stakes decisions” has no effect when the system is repurposed for loan approvals without technical restrictions. Accountability requires operational integration: monitoring dashboards, alert thresholds triggering at 1.25\(\times\) subgroup disparity, incident response procedures, and access controls preventing deployment beyond validated use cases.
Fallacy: Responsible AI is primarily a legal compliance issue.
Teams treat responsibility as external oversight rather than engineering practice. Engineering decisions made months before legal review constrain the solution space more than any compliance assessment. Architecture selection determines what fairness interventions are feasible (adding demographic tracking to a six-month-old pipeline costs 3–4\(\times\) the initial implementation). Data pipeline design establishes whether disaggregated evaluation is even possible. As Section 1.2.5 establishes, systems designed with responsibility as an engineering objective enable efficient validation; systems where responsibility is added at late-stage review face 6–12 months of redesign or deployment with documented risks.
Pitfall: Measuring the environmental impact of training but not inference.
Public discourse focuses on the carbon cost of training runs, and engineers naturally follow this framing when assessing environmental responsibility. The TCO analysis in Section 1.4.3 reveals why this focus is misplaced: inference-to-training cost ratios can exceed 40:1 over a model’s operational lifetime. A model trained once but served millions of times daily has its environmental footprint dominated by inference, not training. For the recommendation system analyzed in Table 16, training accounts for just 2 percent of three-year costs while inference accounts for 73 percent. The carbon ratio is even more lopsided in this example, with inference emitting about 63:1 as much CO2 as training. Engineers who optimize training efficiency while ignoring per-query inference costs address the smaller term in a lopsided equation, leaving the dominant source of environmental impact unexamined.
Self-Check: Question
A deployed loan-approval model reports 85 percent aggregate accuracy, but disaggregated evaluation shows qualified applicants from one demographic group have a true-positive rate 30 percentage points lower than another group. Which pitfall from the section does this outcome most directly illustrate?
- The mistaken belief that fairness can be assessed from aggregate metrics alone, because strong overall accuracy masks the subgroup disparity that only disaggregated evaluation surfaces.
- The mistaken belief that documentation automatically enforces deployment constraints, so a written model card prevents misuse even when no technical control blocks it.
- The mistaken belief that removing sensitive attributes from training data always eliminates bias, so explicit-attribute exclusion guarantees proxy-free predictions.
- The mistaken belief that training costs dominate lifecycle cost, which leads teams to over-optimize training at the expense of inference.
A team proposes removing race and gender features from their model, then deploying without further fairness evaluation because “the model cannot discriminate on attributes it does not see.” Drawing on the Amazon recruiting and Optum healthcare-cost cases from the chapter, explain why this reasoning creates false confidence rather than eliminating bias, and identify the specific engineering work still required.
True or False: Because a well-written model card explicitly states intended use and excluded use cases, teams that publish comprehensive model cards can treat deployment-scope compliance as handled without additional technical controls.
True or False: For most successful production ML systems, reporting the carbon emissions from training runs accurately characterizes the system’s long-term environmental burden.
Summary
Responsible engineering is ML systems engineering done completely, not a separate discipline. The chapter traced a path from failure diagnosis through prevention to enforcement, beginning with the responsibility gap (the distance between technical performance and responsible outcomes) and demonstrating how proxy variables, feedback loops, and distribution shift cause systems to harm users while meeting every conventional metric. The engineering response includes checklists that systematize predeployment assessment, fairness metrics that make disparities measurable, explainability mechanisms that satisfy regulatory and stakeholder requirements, and monitoring infrastructure that detects silent failures before they accumulate harm.
The key insight unifying these tools is that translating responsibility concerns into measurable properties makes them tractable. “Fairness gap <5 percent across groups” is actionable; “be fair” is not. This translation extends beyond fairness: efficiency becomes carbon accounting and TCO analysis, where a 20 percent latency reduction through quantization saves USD 304K and eliminates 19 tons of CO2. Documentation becomes model cards with explicit intended use and known limitations. Governance becomes access control, lineage tracking, and audit infrastructure that makes compliance demonstrable rather than aspirational. At every level, the same pattern holds: abstract ethical obligations become concrete engineering requirements that can be specified, tested, monitored, and enforced.
Key Takeaways: Reliable for whom?
- Correctness is insufficient: A model can achieve 95 percent accuracy while showing 43\(\times\) error rate disparities across demographic groups. Aggregate metrics conceal failures that disaggregated, intersectional evaluation reveals.
- Tractable responsibility: “Fairness gap <5 percent across groups” is actionable; “be fair” is not. The Pareto frontier makes fairness-accuracy trade-offs explicit and quantifiable for stakeholder decisions.
- Efficiency–responsibility alignment: A 4\(\times\) more efficient model uses 4\(\times\) less energy, costs 4\(\times\) less, and enables 4\(\times\) more organizations to deploy. Inference costs dominate TCO by 40:1 over training, making per-query optimization the highest-leverage responsibility intervention.
- Checklist discipline: The aviation-inspired checklist approach transforms abstract fairness concerns into concrete, phase-gated deployment questions that teams must answer before shipping.
- Proactive monitoring: Biased systems continue operating without alerts because degraded predictions look identical to normal predictions. Monitoring must track outcome distributions across demographic groups, not just aggregate accuracy.
- Governance as infrastructure: Data lineage, audit trails, access controls, and privacy-preserving techniques must be built into pipelines from inception. Regulations like GDPR impose specific technical capabilities (right to erasure, right to explanation) that cannot be retrofitted.
- Enforceable documentation: Model cards and datasheets translate assumptions, intended use, and known limitations into auditable artifacts that regulators and stakeholders can verify.
The responsible engineering practices developed in this chapter are integral components of complete engineering, not external constraints layered onto technical work. Systems that ignore fairness, efficiency, transparency, or governance are technically incomplete. The same rigor applied to latency budgets and memory constraints must extend to demographic parity, environmental impact, and regulatory compliance. Engineers who integrate these considerations from system inception build systems that are not only more ethical but more robust, more maintainable, and more likely to succeed in production.
What’s Next: From technique to philosophy
In Conclusion, we assemble these pieces into a coherent philosophy of engineering excellence. Where this chapter addressed whether systems serve everyone fairly and justify their resource consumption, the conclusion takes on the broadest concern of all: what it means to build ML systems well, in every dimension that the word encompasses.
Self-Check: Question
After reading the chapter, which statement best captures the summary’s claim about how responsible engineering relates to traditional systems engineering?
- Responsible engineering is primarily a legal and ethical overlay that engineering teams apply after the technical system is feature-complete.
- Responsible engineering is a specialty concern that matters only for high-risk regulated domains such as healthcare and criminal justice.
- Responsible engineering is ML systems engineering done completely: a system that ignores fairness, efficiency, transparency, or governance is technically incomplete, not merely ethically imperfect.
- Responsible engineering replaces performance optimization with ethical review, so teams adopting it trade throughput and latency for fairness and transparency.
The summary argues that responsibility concerns become tractable only when translated into measurable engineering invariants. Explain what this means by contrasting a vague principle with a specific invariant, and describe how the invariant integrates into an existing monitoring workflow.
The summary argues that earlier optimization techniques taught in the book serve a “second master” beyond performance. Which pairing most precisely reflects that dual-purpose claim?
- Monitoring primarily detects latency regressions, so fairness monitoring requires entirely separate infrastructure that does not share code paths with reliability monitoring.
- Hardware acceleration improves throughput and energy efficiency at the chip level, but grid-scale carbon impact depends purely on regulatory-policy decisions that engineers cannot influence through technical choices.
- Quantization yields sustainability benefits (lower energy per inference) but those benefits are independent of accessibility, since cheaper hardware deployment is a product-management concern rather than a consequence of compute reduction.
- Quantization, pruning, and monitoring improve throughput and latency while simultaneously reducing carbon per query, broadening deployment to lower-cost hardware, and surfacing silent subgroup disparities — the same techniques serve performance and responsibility through shared mechanisms.
Self-Check Answers
Self-Check: Answer
A hiring model meets its latency SLA, maintains 99.9 percent availability, and reports 87 percent aggregate accuracy, yet it systematically rejects qualified applicants whose resumes contain the word “women’s.” Applying the section’s verification-versus-validation framing, which diagnosis best fits this outcome?
- The system passed verification but failed validation: it met every stated requirement while the requirement itself failed to capture the responsible outcome the organization needed.
- The system failed verification because any unfair outcome is by definition a technical defect of the implementation.
- The failure is primarily an operational reliability issue that responsible engineering practices address only after the serving pipeline becomes unstable.
- The root cause is insufficient model capacity, so scaling up parameters would remove the disparity without changing the specification.
Answer: The correct answer is A. The model satisfied its loss function and its availability targets, so verification succeeded in the systems-engineering sense, but the requirement itself encoded historical bias rather than the organization’s true hiring goal. The capacity-based answer makes the wrong diagnosis: a larger model would optimize the same flawed objective more faithfully, not less. The reliability-based answer conflates outage response with specification correctness, which is exactly the category error the section warns against.
Learning Objective: Classify a concrete ML deployment failure as verification-success-with-validation-failure and distinguish it from reliability or capacity issues.
A team argues that a one-time ethics review before launch is sufficient because their model achieves strong aggregate accuracy and passes all latency checks. Using the section’s MLOps analogy, explain why responsible engineering must instead be structured as a control loop, and give one specific measurement the one-time review would miss.
Answer: MLOps is the control loop for reliability because model performance degrades as data distributions drift; responsible engineering is the control loop for safety because outcome quality degrades as downstream populations and proxies drift, and both degradations are silent to the dashboards engineers already watch. A specific signal the one-time review misses is subgroup-level outcome disparity over time: a model reviewed at launch with 87 percent aggregate accuracy can develop a 30-point true-positive-rate gap for a minority subgroup months later without moving any latency or availability metric. The practical consequence is that responsibility requires the same ongoing measurement, feedback, and intervention infrastructure as latency SLOs, not a sign-off meeting that closes the loop.
Learning Objective: Explain the MLOps-to-responsibility control-loop parallel and identify a specific fairness measurement a one-time review cannot provide.
True or False: Because machine learning systems are built from modular software components, a fairness defect originating in the training data can be isolated to a single module and fixed without architectural change, the way a null-pointer exception can be patched in one function.
Answer: False. The section’s central structural point is that ML data flows through shared representations, so a biased training signal propagates through every prediction the system makes rather than remaining local. Unlike a null-pointer bug, the defect is encoded in the learned weights themselves, so fixing it requires data-pipeline, objective, and evaluation changes across the D·A·M axes, not a localized patch.
Learning Objective: Distinguish localized software bugs from architecture-level ML failures and justify why specification-induced harm propagates across shared representations.
Self-Check: Answer
Amazon’s engineers removed explicit gender indicators from the recruiting model’s features, retrained, and found the system still discriminated against resumes from all-women’s colleges. Which diagnosis best explains why the explicit-attribute removal did not fix the harm?
- The fix was sound in principle; the system only needed additional bias-mitigation training epochs for the gender signal to fade from the learned weights.
- College names, activity descriptions, and career-gap patterns remained as proxy variables that carried the same demographic signal the removed gender feature had carried.
- The problem was deployment-time distribution shift in the applicant pool rather than bias in the original training signal.
- The problem was an optimization-objective mismatch that a different gradient-descent variant would have corrected during convergence.
Answer: The correct answer is B. Protected attributes can be reconstructed from correlated features even when the explicit label is absent, so a model trained on a dataset containing college names and activity descriptions recovers gender indirectly and preserves the original discriminatory pattern. The deployment-drift answer misidentifies the failure mode: Amazon’s harm is a biased training signal that predates deployment, not an environmental shift. The optimizer-choice answer is a category error because changing the optimizer does not remove the information content of the proxy features from the training set.
Learning Objective: Analyze how proxy variables preserve discrimination after explicit protected-attribute removal and distinguish this failure mode from deployment-time drift.
A hospital’s sepsis prediction model continues to emit confident recommendations after an EHR update changes how vital signs are recorded, yet clinicians observe deteriorating outcomes for a subset of patients. All dashboards stay green. Walk through why this is a silent failure, identify two specific monitoring signals that would have caught it, and state the systems consequence for how teams instrument production ML.
Answer: The failure is silent because the model’s confidence scores, latency, and uptime dashboards all rely on the output distribution looking the same as training, but an EHR change shifts the input distribution, so the model emits normal-looking predictions on inputs that are effectively out-of-distribution. Two specific signals that would have caught this: input-feature drift detection (for example, Jensen-Shannon divergence between training and current feature distributions crossing a 0.1 threshold) would have flagged the EHR change, and disaggregated outcome monitoring against ground-truth sepsis diagnoses would have shown the subgroup-level accuracy collapse before the aggregate moved. The systems consequence is that production responsibility monitoring must instrument the input pipeline and per-subgroup outcomes, not just confidence and latency, because dashboards that track only the system’s self-reported health cannot see distribution-shift failures.
Learning Objective: Analyze a distribution-shift silent failure on a concrete clinical scenario and specify the monitoring signals that distinguish environmental failures from healthy operation.
A recommendation team reports that engagement clicks rose 20 percent after deploying a new ranker, but month-over-month user satisfaction surveys dropped five percent and 30-day retention fell three percent. The team’s director asks how to detect or prevent this class of failure before it recurs. Which engineering intervention best fits the section’s alignment-gap framing?
- Scale the model two-fold: a larger model will learn a richer representation of satisfaction and close the gap automatically.
- Hold out a random counterfactual slice of users at deployment, measure true-outcome metrics (satisfaction, retention) on that slice periodically, and trigger rollback when the proxy-true gap widens beyond a preset threshold.
- Increase the weight of the clicks loss term: because the proxy correlates with the true goal initially, maximizing it harder will restore the lost correlation.
- Retrain on more data: with enough examples, gradient descent will discover the satisfaction signal implicitly even when it is not in the training labels.
Answer: The correct answer is B. The section’s alignment-gap analysis is a Goodhart-style decoupling between a measurable proxy (clicks) and an unobservable true goal (satisfaction); the only way to detect the decoupling is to periodically re-calibrate the proxy against the true outcome using a counterfactual holdout. Scaling up the model or reweighting the clicks loss makes the proxy-true gap worse by optimizing the proxy more aggressively. Retraining on more data does not help because the training labels do not contain satisfaction information, so more examples cannot surface a signal the loss function was never given.
Learning Objective: Apply the alignment-gap mechanism to a concrete recommender scenario and select the engineering intervention that re-anchors a proxy metric to its unobservable true goal.
A lending team generates paired test applications that differ only in the applicant’s first name (“John” vs “Jamal”) while holding income, credit history, and debt constant, then compares approval probabilities. Which responsible-testing method from the section are they applying, and what failure mode does it surface?
- Boundary testing, which probes behavior at the edges of the input distribution where training data is sparse.
- Slice-based evaluation, which partitions the test set into subgroups and reports per-slice aggregate accuracy.
- Stakeholder red-teaming, which relies on affected community members to propose adversarial scenarios.
- Invariance testing, which verifies that predictions remain stable when a feature the model should ignore is perturbed.
Answer: The correct answer is D. Invariance testing explicitly checks whether predictions change under a perturbation of an irrelevant attribute while holding task-relevant features fixed, which is precisely the counterfactual-pair construction the lending team is using. Slice-based evaluation answers a different question — per-subgroup aggregate metrics — and cannot isolate the causal effect of the name change. Boundary testing probes sparse regions of the input space, not counterfactual invariance. Red-teaming identifies scenarios to test but does not define the test construction itself.
Learning Objective: Classify responsible-testing methods by their construction and the specific failure mode each is designed to expose.
True or False: Once a model’s architecture, loss function, demographic-attribute collection, and monitoring pipeline have been fixed, a later ethics-board review can still implement equally effective fairness interventions as engineers could have at design time.
Answer: False. The section shows that each early architectural decision forecloses remediation options downstream: a loss function chosen without fairness constraints cannot be retrained without starting over, an architecture chosen without interpretability cannot be explained post hoc, and a data pipeline that omits demographic attributes cannot support disaggregated evaluation at all. By review time, the ethics board’s choices collapse to accept, reject, or rebuild — which is why Amazon’s review required cancelling the project rather than patching it.
Learning Objective: Evaluate why late-stage review cannot substitute for engineering-time responsibility decisions, grounded in the D·A·M architectural-foreclosure mechanism.
Self-Check: Answer
A team needs a statistically valid test set of 10,000 face images for a subgroup that makes up 1 percent of the user base to detect a one-percent performance gap with 95 percent confidence. Using the section’s representation statistics, what total sample collection does random sampling require, and what does this imply for the fairness evaluation workflow?
- About 100,000 total images, because confidence intervals shrink roughly linearly with the combined dataset size regardless of subgroup prevalence.
- About 1,000,000 total images, because subgroup confidence depends on subgroup sample count, so random collection requires a 100x multiplier relative to the target and makes intentional stratified collection an engineering prerequisite.
- About 10,000 total images, because the target test-set size is already fixed and subgroup composition is handled automatically by the model’s training procedure.
- Sample-size reasoning applies only to training data; evaluation confidence scales with the number of gradient-update steps, not with the subgroup sample count.
Answer: The correct answer is B. Dividing the target 10,000 subgroup samples by the 0.01 prevalence yields 1,000,000 total samples — the 100x multiplier the section derives — which makes natural-distribution sampling infeasible at production scale and forces intentional stratified collection through targeted outreach or active learning. A 100,000-image estimate ignores that subgroup confidence intervals scale with subgroup sample count, not overall dataset size. Claiming evaluation escapes the constraint confuses training data with test data: the subgroup confidence interval is purely a statistical property of the held-out test set.
Learning Objective: Apply representation statistics to derive the 100x data multiplier and justify stratified collection as a fairness-evaluation engineering requirement.
A team argues they will write their model card after launch so it can accurately reflect observed behavior. Explain why the section calls this a guard-rail failure, and describe one specific scope-creep scenario that a predeployment model card would have blocked but a post-launch card would not.
Answer: A model card written before deployment constrains what the system is allowed to do by specifying intended use, excluded use cases, and the demographic factors under which performance was validated, so it operates as an enforcement artifact that downstream teams must satisfy before repurposing the model. Written after launch, the card becomes a historical summary that records whatever the deployment already does, which cannot prevent scope creep that has already occurred. A concrete scenario: a vision model validated only for consumer photo organization with a card specifying “not validated for high-stakes screening” can be automatically blocked from reuse in a security application, whereas a card written six months into the security deployment would merely describe the security use case rather than prevent it. The systems consequence is that the estimated 40 to 60 percent of deployments that exceed their documented scope do so through gradual expansion that only an up-front card can arrest.
Learning Objective: Explain why model-card timing determines whether it functions as a deployment constraint or a retrospective record, and identify a concrete scope-creep scenario this timing controls.
In the loan-approval worked example, Group A (majority) has a true positive rate of 90 percent and Group B (minority) has a true positive rate of 60 percent, while both groups share the same false positive rate of 20 percent. Evaluating each fairness criterion against these numbers, which statement is correct?
- Demographic parity is satisfied because the false positive rates match across groups.
- Equal opportunity is violated by the 30-point true-positive-rate gap, and equalized odds is also violated because equalized odds requires both true-positive-rate and false-positive-rate equality, so matching false positive rates alone is not sufficient.
- Equalized odds is satisfied because one of its two component rates matches across groups.
- Only calibration is implicated, because true-positive-rate disparities affect model accuracy rather than fairness.
Answer: The correct answer is B. Equal opportunity requires equal true-positive rates among qualified applicants, so a 30-point gap violates it directly — qualified minority applicants face a 30-point higher rejection rate than equally qualified majority applicants. Equalized odds requires both true-positive-rate and false-positive-rate equality, and the shared false-positive rate cannot rescue the criterion when the true-positive-rate component is violated. Demographic parity is about equal approval rates, not equal error rates, so matching false-positive rates is not its criterion. The calibration-only framing misreads the problem: true-positive-rate disparities are fairness violations regardless of their aggregate-accuracy effect.
Learning Objective: Diagnose equal-opportunity and equalized-odds violations directly from confusion-matrix statistics and distinguish them from demographic parity and calibration.
Stakeholders ask a hiring team to close a 20-percentage-point true-positive-rate gap between two groups by lowering the decision threshold for the disadvantaged group. Using the Pareto-frontier framing and the price-of-fairness calculation from the section, analyze what the team should present to stakeholders and why threshold adjustment alone is a design choice, not a technical fix.
Answer: Lowering the threshold for the disadvantaged group increases that group’s true-positive rate but also its false-positive rate, which in the section’s hiring example translates to roughly a 5-percentage-point rise in false positives and about a 1.4-percent aggregate utility loss under the stated assumptions: $100k successful-hire value, $50k bad-hire cost, a 50-percent qualified-applicant base rate, and a disadvantaged group that is 30 percent of the applicant pool. The team should present the Pareto frontier to stakeholders: each candidate threshold traces out a specific (accuracy, disparity) point, and no reweighting can move the system off the frontier — only choosing where on the frontier to sit. The practical consequence is that threshold adjustment is a values decision expressed through engineering, not a technical patch: the engineer’s job is to make the trade-off quantitative and legible so stakeholders can pick the point aligned with organizational priorities rather than discovering the trade-off after deployment.
Learning Objective: Quantify the price-of-fairness trade-off for a concrete threshold-adjustment scenario and justify why Pareto-frontier presentation is the correct engineering deliverable to stakeholders.
A European lender plans to deploy a deep neural network that automates credit decisions affecting hundreds of thousands of applicants per year. Given EU AI Act high-risk classification and GDPR Article 22 obligations as described in the section, which architectural consequence follows most directly?
- Because deeper models are more accurate, explainability engineering can be deferred until after legal approval closes.
- Aggregate fairness metrics alone are sufficient because individual applicant explanations are irrelevant in financial decisions.
- The deployment architecture must be designed at inception to support per-applicant explanations, substantive human review of automated decisions, and audit-trail logging, because adverse-action and Article 22 substantive-review obligations are enforced as technical requirements with 35M EUR or 7-percent-global-turnover penalties.
- EU regulation applies primarily to foundation models, so a loan classifier with fewer than a billion parameters can be deployed without explainability infrastructure.
Answer: The correct answer is C. Credit decisions are high-risk under EU AI Act Annex III regardless of model size, and Article 22 requires substantive human review for automated decisions with significant effects, so the architecture must ship from day one with per-applicant explanation capabilities (to satisfy adverse-action notice requirements), human-oversight interfaces, and logging infrastructure that supports audit. Aggregate fairness metrics do not discharge the per-applicant recourse obligation, which is individual-level by construction. The size-based framing misreads Annex III: risk classification is based on deployment context, not model architecture, so a logistic regression deciding credit carries the same obligations as a large transformer.
Learning Objective: Analyze how high-stakes regulatory obligations translate into specific architectural capabilities that must be engineered in at system inception rather than retrofitted.
Self-Check: Answer
A team can deploy either a full-precision model or a quantized version that preserves task accuracy while cutting inference compute by roughly 4x. According to the section, why does this efficiency choice count as a responsibility decision rather than purely a performance decision?
- Quantization is primarily a responsibility tool because it automatically reduces fairness disparities by making all user groups equally cheap to serve.
- Quantization reduces compute per inference, which simultaneously shrinks carbon emissions in proportion, lowers serving dollar cost, and lowers hardware barriers so smaller organizations and edge devices can deploy the model.
- Quantization is a pure performance optimization that should be evaluated separately from responsibility, because fairness, carbon, and cost belong to distinct engineering layers with different owners.
- Quantization matters mainly for training-time energy: production inference is usually a minor fraction of lifecycle resource use, so the responsibility payoff is small.
Answer: The correct answer is B. The section’s efficiency-as-responsibility argument is that a single intervention (reducing compute per inference) pays out simultaneously across three channels — carbon (4x fewer emissions per query), dollar cost (4x lower serving bill), and accessibility (the model fits cheaper hardware or devices that would otherwise be priced out). The “separate layers” answer is the misconception the section exists to correct: splitting efficiency from responsibility misses the unification. The fairness-automation answer conflates cost-per-query with fairness, which the section explicitly keeps distinct. The training-dominance answer contradicts the 40:1 inference-to-training ratio in the TCO analysis.
Learning Objective: Justify why efficiency interventions serve environmental, economic, and accessibility responsibilities simultaneously rather than being a separable performance concern.
A wearable device has a 500 mW sustained power budget and a 500 ms end-to-end inference latency requirement. Using the section’s deployment-comparison data (TinyML at roughly 50 mW / 200 ms, MobileNetV2 at roughly 1.2 W / 40 ms, EfficientNet-B0 at roughly 1.8 W, ResNet-50 much larger), which model selection is the correct responsible-engineering choice, and why?
- ResNet-50, because larger models achieve better energy efficiency per accuracy point once their throughput is amortized through batching.
- MobileNetV2, because 1.2 W is close enough to the 500 mW target that the gap is operationally negligible on modern battery-management hardware.
- TinyML model, because its 50 mW power draw fits 10x under the budget and its 200 ms latency fits under the 500 ms requirement, so it is the only option that satisfies both constraints simultaneously.
- EfficientNet-B0, because its smartphone-grade footprint guarantees it also fits wearable constraints once the form factor is reduced.
Answer: The correct answer is C. Only the TinyML model satisfies both the 500 mW power ceiling (at 50 mW, a 10x margin) and the 500 ms latency ceiling (at 200 ms); every other option exceeds the power budget by at least 2x. The MobileNetV2 answer misreads the power constraint — a wearable cannot sustain 1.2 W without thermal throttling and rapid battery depletion, so “close enough” is quantitatively wrong by a factor of 2.4. The smartphone-to-wearable extrapolation is the common mistake the section warns against: wearable budgets are an order of magnitude tighter than smartphones on sustained draw. Batching arguments do not rescue ResNet-50 on a device that serves one query at a time.
Learning Objective: Apply edge-deployment power and latency constraints to select a model architecture that satisfies both budgets and reject the smartphone-to-wearable extrapolation.
Using the section’s three-year TCO breakdown (training ~2 percent, inference ~73 percent, operations ~25 percent for a recommendation system serving 200M daily queries), a team proposes two optimization options: Proposal 1 is a 50 percent reduction in training wall-clock time, and Proposal 2 is a 20 percent reduction in per-query inference latency via quantization. Explain which proposal has higher leverage on both dollar cost and carbon, and give the rough dollar-savings ratio between them.
Answer: The inference latency reduction has higher leverage in both dimensions because inference dominates lifecycle cost at roughly 73 percent of the 3-year total while training sits at only 2 percent. A 20 percent cut on the 73 percent term saves roughly 14.6 percent of total cost, whereas a 50 percent cut on the 2 percent term saves only about 1 percent of total cost, giving a dollar-savings ratio near 15-to-1 in favor of inference optimization. The carbon ratio is even more lopsided in this scenario: the same 20 percent inference reduction saves about 25 times as much CO2 as the 50 percent training-time reduction because inference consumes far more GPU-hours over the deployment lifetime. The practical consequence is that on inference-dominated workloads, per-query optimization is the highest-leverage responsibility intervention available and should capture the majority of engineering investment.
Learning Objective: Compare two optimization proposals using TCO framing to quantify which intervention has higher leverage on dollar cost and carbon for inference-dominated production systems.
True or False: For an identical model and serving workload, migrating deployment from a carbon-intensive cloud region to one powered by abundant renewable energy can reduce inference emissions more than a one-time modest algorithmic efficiency improvement.
Answer: True. The section notes cloud region choice can yield roughly a 5x carbon reduction while typical algorithmic tweaks fall in the low-percent range, so when the algorithmic gain is modest the infrastructure choice dominates emissions. Carbon intensity of the underlying grid is therefore a first-class infrastructure parameter engineers must surface alongside compute efficiency, not a post-hoc accounting detail.
Learning Objective: Evaluate how grid-carbon-intensity infrastructure choices can outweigh algorithmic efficiency gains in overall emissions for the same workload.
Training GPT-3 consumed roughly 1,287 MWh of electricity. At a US-grid average carbon intensity of roughly 0.429 kg CO2 per kWh, what does the section identify as the dominant responsible-engineering lever for reducing the footprint of future foundation-model training runs?
- Reducing model size to under one billion parameters, accepting the corresponding accuracy loss, because parameter count is the only significant driver of training energy.
- Improving accelerator utilization η during training so that the same 1,287 MWh produces more useful FLOPs, combined with carbon-aware scheduling that runs intensive jobs when renewable supply is abundant and selecting regions with lower grid-carbon intensity.
- Deferring all training until grid carbon intensity reaches zero, since any non-zero intensity produces emissions that cannot be justified ethically.
- Switching the entire training pipeline from FP32 to FP16 without other changes, because numerical precision alone accounts for the bulk of training energy use.
Answer: The correct answer is B. The section’s quantitative analysis identifies two stackable infrastructure levers: efficiency (η improvements so more of the 1,287 MWh becomes useful FLOPs rather than memory stalls) and carbon-aware scheduling and region selection (which can yield roughly 5x reductions independent of the algorithm). Parameter reduction is one lever but not the only one, and treating it as sole driver ignores that utilization dominates effective energy per useful FLOP. The zero-carbon answer is a category mistake — it is a moral absolutism, not an engineering intervention. The FP16-only answer overstates precision’s share of energy: precision matters, but the section places it alongside utilization and grid selection, not above them.
Learning Objective: Identify the dominant infrastructure-layer responsibility levers (efficiency and carbon-aware scheduling) for large-scale training energy and reject single-lever framings.
Self-Check: Answer
In 2023 Meta received a 390M EUR fine not for a data breach but for insufficient governance infrastructure to demonstrate lawful processing. Which diagnosis best captures why the section frames data governance as an enforcement mechanism rather than a policy document?
- Governance replaces the need for model monitoring once regulators sign off on the data pipeline, because certification transfers ongoing responsibility to the certifier.
- Governance is primarily about publishing external-facing datasheets and model cards so that readers outside the organization can assess the system.
- Policy claims become demonstrable only when access controls, privacy mechanisms, lineage tracking, and audit logs make each requirement technically enforceable across the data lifecycle — otherwise compliance is an assertion rather than evidence.
- Governance applies only to raw storage, since derived features, model artifacts, and deployment workflows are downstream and fall outside the data lifecycle.
Answer: The correct answer is C. Meta’s fine demonstrates the section’s structural point: governance that exists only as policy cannot withstand audit because the organization cannot produce evidence of enforcement. The architecture must record who accessed data, what transformations produced each feature, and which model versions derived from which training runs — policy without these technical controls is unverifiable. The certification-handoff answer is wrong because regulatory certification does not transfer ongoing compliance. The datasheet-only answer confuses documentation with enforcement; model cards are necessary but do not control access. The raw-storage-only answer contradicts the section’s explicit scope: governance spans features, models, and deployment workflows, not just raw data.
Learning Objective: Explain why data governance must be implemented through enforceable technical infrastructure and distinguish this framing from documentation-only or raw-storage-only views.
A European user of a voice-assistant service invokes GDPR Article 17 right-to-erasure. Explain why a manual search across storage systems is both unreliable and too slow to satisfy the request, and describe what automated infrastructure the compliance architecture must instead provide.
Answer: Satisfying Article 17 requires locating not only the user’s raw audio recordings but also every derived artifact that depended on that data — feature-store entries, embedding caches, fine-tuned model checkpoints, and audit logs — across storage layers, feature stores, training jobs, and deployed model versions. A distributed ML pipeline fans data across systems that a manual trace cannot visit reliably within regulatory time limits, and any missed artifact is itself a compliance failure. The architecture must instead provide an automated lineage graph that links every source record to its downstream derivations and a deletion workflow that traverses this graph to remove or invalidate each dependent artifact. The practical consequence is that compliance is an infrastructure problem: teams that rely on ad-hoc search either miss artifacts (risking fines) or take weeks to respond (violating the regulation’s timeline), whereas a lineage-backed deletion pipeline makes the request a routine automated operation.
Learning Objective: Analyze why distributed ML pipelines make manual deletion infeasible and identify the lineage-and-automation infrastructure that right-to-erasure compliance requires.
The Lighthouse KWS system is an always-listening keyword-spotting voice assistant deployed in users’ homes. Which architectural combination best reflects the section’s privacy-by-design approach for this deployment, and why?
- Stream all ambient audio to a cloud service that applies strong centralized privacy controls after collection, since centralized processing allows more sophisticated mechanisms than any edge device can run.
- Run wake-word detection on-device, transmit only aggregated or federated updates rather than raw recordings, and enforce automatic retention and deletion policies on any audio that must be retained, so the system minimizes the personal data exposed in the first place.
- Retain raw audio indefinitely on secure cloud storage, because the future retraining value of long-horizon voice data outweighs privacy concerns when access is properly encrypted.
- Rely on role-based access control as the sole privacy mechanism, since privacy concerns reduce to limiting who can query the data and RBAC solves exactly that problem.
Answer: The correct answer is B. The section’s privacy-by-design architecture combines three complementary moves — on-device processing (raw audio never leaves the device in the common case), federated-style minimization (only aggregated signals cross the network), and retention limits (any retained audio has a bounded lifetime) — so the attack surface is small by construction rather than by policy. Centralized cloud collection inverts the principle: it maximizes the data exposed before applying any protection, so a breach or insider access exposes more. Indefinite retention treats future training value as a blank check, which the section explicitly rejects. RBAC-only misreads the threat model: RBAC limits who can query data, but privacy also requires limiting what even authorized actors can learn about individuals, which is a separate problem that techniques like differential privacy and data minimization address.
Learning Objective: Identify the privacy-by-design architectural pattern for always-listening systems and distinguish privacy minimization from access-control mechanisms.
A teammate argues that security, privacy, and audit are essentially the same concern because each restricts data access. Using the section’s governance stack, distinguish the operational role of each and give one concrete failure mode that would not be caught if the other two were fully implemented but that mechanism were missing.
Answer: Security answers who can reach the data at all: access controls, authentication, and encryption define the perimeter within which all other mechanisms operate. Privacy answers what information authorized actors can learn about individuals: differential privacy, minimization, and aggregation limit inference even when access is legitimate. Audit answers who actually did what: logs of access and transformation events create the accountability trail that makes the other two verifiable under scrutiny. A system with strong security and privacy but no audit cannot respond to a regulatory subpoena that asks which employee accessed which records on which date — the access happened legitimately, the data was appropriately anonymized, but the organization cannot prove either claim and fails the audit. Symmetrically, strong security plus audit without privacy still leaks individual-level information to every authorized data scientist, and strong privacy plus audit without security lets unauthorized actors bypass the whole stack. The mechanisms are complementary accountability layers, not redundant restrictions.
Learning Objective: Distinguish the operational roles of security, privacy, and audit mechanisms in the governance stack and identify a concrete failure mode specific to each missing mechanism.
True or False: Because GDPR Article 17 (right-to-erasure) penalties are capped at modest administrative amounts, an ML team can reasonably defer building automated lineage infrastructure until the first deletion request arrives.
Answer: False. GDPR imposes fines up to the greater of 20M EUR or 4 percent of global annual revenue for non-compliance, a scale sufficient to threaten corporate solvency, and the section’s Meta example (390M EUR in 2023) demonstrates that governance-infrastructure deficiencies — not data breaches — drive the largest penalties. Deferring lineage infrastructure until the first request arrives also makes timely compliance infeasible across distributed artifacts, compounding the regulatory risk.
Learning Objective: Evaluate the quantitative regulatory risk that makes up-front lineage infrastructure a prerequisite rather than an optional engineering investment.
Self-Check: Answer
A deployed loan-approval model reports 85 percent aggregate accuracy, but disaggregated evaluation shows qualified applicants from one demographic group have a true-positive rate 30 percentage points lower than another group. Which pitfall from the section does this outcome most directly illustrate?
- The mistaken belief that fairness can be assessed from aggregate metrics alone, because strong overall accuracy masks the subgroup disparity that only disaggregated evaluation surfaces.
- The mistaken belief that documentation automatically enforces deployment constraints, so a written model card prevents misuse even when no technical control blocks it.
- The mistaken belief that removing sensitive attributes from training data always eliminates bias, so explicit-attribute exclusion guarantees proxy-free predictions.
- The mistaken belief that training costs dominate lifecycle cost, which leads teams to over-optimize training at the expense of inference.
Answer: The correct answer is A. The 30-percentage-point true-positive-rate gap under 85 percent aggregate accuracy is the canonical flaw-of-averages failure: the aggregate is a weighted average that hides the minority-group disparity, which only disaggregated evaluation reveals. The documentation-enforcement answer describes a different pitfall about deployment scope creep, not aggregate-metric concealment. The attribute-removal answer is also real but refers to why fairness persists after explicit-attribute removal, which is the next fallacy in the section and does not explain the metric mechanic here. The training-cost answer addresses environmental accounting, not fairness metric reporting.
Learning Objective: Identify the aggregate-metric pitfall when strong overall performance conceals substantial subgroup disparity and distinguish it from other fallacies in the section.
A team proposes removing race and gender features from their model, then deploying without further fairness evaluation because “the model cannot discriminate on attributes it does not see.” Drawing on the Amazon recruiting and Optum healthcare-cost cases from the chapter, explain why this reasoning creates false confidence rather than eliminating bias, and identify the specific engineering work still required.
Answer: Protected attributes remain inferable through correlated proxies that carry the same demographic signal: Amazon’s system reconstructed gender from college names, activity descriptions, and career-gap patterns despite explicit gender removal, and Optum’s system encoded race through healthcare-cost history because unequal system access made cost a de-facto race proxy; correcting the bias would have increased the share of Black patients receiving additional help from 17.7 percent to 46.5 percent. Research shows models recover protected attributes with 70 to 90 percent accuracy from supposedly neutral features like ZIP codes, purchase patterns, and browsing history. The engineering work still required includes causal analysis of which features carry demographic signal, fairness constraints during training (adversarial debiasing or constrained optimization), per-group outcome monitoring in production, and the disaggregated-metric reporting this chapter develops — attribute removal alone is necessary but insufficient, and teams that stop there deploy a model that discriminates while appearing compliant.
Learning Objective: Explain why proxy variables undermine naive attribute-removal approaches and specify the causal-analysis, fairness-constraint, and monitoring work required for actual bias mitigation.
True or False: Because a well-written model card explicitly states intended use and excluded use cases, teams that publish comprehensive model cards can treat deployment-scope compliance as handled without additional technical controls.
Answer: False. The section’s documentation-as-accountability pitfall is exactly this assumption: studies show 40 to 60 percent of production models operate outside their documented scope within 18 months, and a model card specifying “not validated for high-stakes decisions” has no enforcement power when the system is repurposed without access-control or deployment-gate restrictions. Documentation provides transparency but requires paired operational controls — monitoring dashboards, subgroup-disparity alerts, and deployment gates tied to the card’s intended use — to function as enforcement.
Learning Objective: Evaluate why documentation without enforcement fails under scope creep and identify the operational controls that must pair with model cards.
True or False: For most successful production ML systems, reporting the carbon emissions from training runs accurately characterizes the system’s long-term environmental burden.
Answer: False. The section’s TCO analysis shows inference-to-training compute ratios reaching 40:1 over a three-year operational lifetime, so a model trained once and served millions of times daily has its carbon footprint dominated by inference energy, not training. Training-only reporting addresses the smaller term in a lopsided equation, leaving the dominant source of environmental impact unmeasured and unaddressed.
Learning Objective: Evaluate why training-only environmental accounting is misleading for production ML systems and quantify the inference-dominance ratio that drives the misclassification.
Self-Check: Answer
After reading the chapter, which statement best captures the summary’s claim about how responsible engineering relates to traditional systems engineering?
- Responsible engineering is primarily a legal and ethical overlay that engineering teams apply after the technical system is feature-complete.
- Responsible engineering is a specialty concern that matters only for high-risk regulated domains such as healthcare and criminal justice.
- Responsible engineering is ML systems engineering done completely: a system that ignores fairness, efficiency, transparency, or governance is technically incomplete, not merely ethically imperfect.
- Responsible engineering replaces performance optimization with ethical review, so teams adopting it trade throughput and latency for fairness and transparency.
Answer: The correct answer is C. The chapter’s closing thesis is that correctness in ML must extend beyond latency and accuracy to encompass fairness, efficiency, transparency, and governance as measurable properties of a complete system, applied from inception. The legal-overlay answer inverts the chapter’s argument: the Amazon and COMPAS cases show that late-stage review cannot fix architecturally foreclosed problems. The specialty-domain answer is contradicted by the efficiency and TCO material, which applies to every production system regardless of regulatory classification. The replacement framing misreads the chapter: earlier optimization techniques (quantization, pruning, hardware acceleration) serve both masters simultaneously rather than being traded off.
Learning Objective: Identify the summary’s thesis that responsibility is engineering completeness and distinguish it from overlay, specialty-domain, and replacement framings.
The summary argues that responsibility concerns become tractable only when translated into measurable engineering invariants. Explain what this means by contrasting a vague principle with a specific invariant, and describe how the invariant integrates into an existing monitoring workflow.
Answer: A vague principle such as “be fair” gives engineers nothing to implement, test, or monitor, whereas an invariant such as “per-group true-positive-rate disparity <5 percentage points, measured hourly, with automatic rollback if exceeded for 15 minutes” is a concrete target that slots directly into existing SLO infrastructure. The engineering consequence is that responsibility invariants integrate into monitoring the same way latency SLOs do: the fairness dashboard sits next to the p99-latency dashboard, the same alerting and on-call rotations cover both, and the same rollback mechanisms that fire on latency regressions can fire on fairness regressions. The practical implication is that responsibility becomes actionable and auditable only at this level of specification; at the principle level, compliance claims cannot be verified and interventions cannot be triggered.
Learning Objective: Explain how concrete measurable invariants make responsibility concerns actionable by integrating into existing SLO and monitoring workflows.
The summary argues that earlier optimization techniques taught in the book serve a “second master” beyond performance. Which pairing most precisely reflects that dual-purpose claim?
- Monitoring primarily detects latency regressions, so fairness monitoring requires entirely separate infrastructure that does not share code paths with reliability monitoring.
- Hardware acceleration improves throughput and energy efficiency at the chip level, but grid-scale carbon impact depends purely on regulatory-policy decisions that engineers cannot influence through technical choices.
- Quantization yields sustainability benefits (lower energy per inference) but those benefits are independent of accessibility, since cheaper hardware deployment is a product-management concern rather than a consequence of compute reduction.
- Quantization, pruning, and monitoring improve throughput and latency while simultaneously reducing carbon per query, broadening deployment to lower-cost hardware, and surfacing silent subgroup disparities — the same techniques serve performance and responsibility through shared mechanisms.
Answer: The correct answer is D. The chapter’s synthesis is that a single technique often pays out along multiple dimensions because the underlying mechanism (fewer bytes moved, fewer cycles spent, faster subgroup-metric computation) simultaneously reduces energy per query, lowers the hardware cost floor for deployment, and makes real-time fairness monitoring feasible. The monitoring-as-separate-infrastructure answer contradicts the chapter’s argument that subgroup-disparity dashboards extend existing reliability monitoring rather than replacing it. The sustainability-separated-from-accessibility answer misses the three-channel unification: reducing compute per inference directly lowers the hardware cost floor. The policy-only carbon answer misreads the chapter’s efficiency-as-responsibility argument — grid carbon intensity matters, but chip-level efficiency multiplies against it rather than being irrelevant to it.
Learning Objective: Analyze how prior optimization and monitoring techniques serve both performance and responsibility objectives through shared mechanisms rather than through separable work.